IA44-A User Manual: Difference between revisions
(Created page with " Connecting with the device to the System (Laptop/Desktop) To log in to SILBO_IA44-A by connecting the router to your laptop or desktop via LAN or using Wi-Fi, please follow the steps below. '''Connecting via LAN:''' Connect your laptop's LAN port to one of the router's LAN interfaces. Ensure that you select any LAN interface (there is one available) while making sure the WAN interface is not used. ...") |
|||
| (8 intermediate revisions by the same user not shown) | |||
| Line 16: | Line 16: | ||
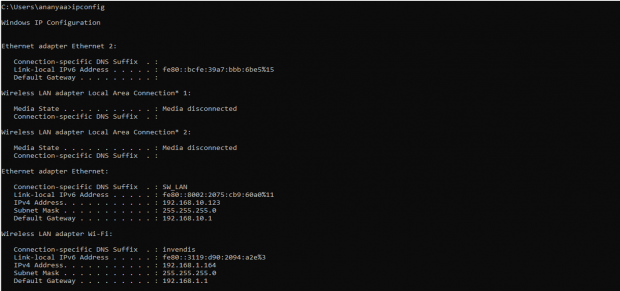
Type the command '''Ipconfig''' | Type the command '''Ipconfig''' | ||
[[File:How_to_connect_with_the_SILBO_RB44_application.png|alt=How to connect with the SILBO RB44 application|frameless|620x620px]] | |||
It will provide the Ip address/url of that device through which the application can be accessed. | |||
[[File:Connecting_via_LAN_RB44.png|frameless|620x620px]] | |||
== Log In == | |||
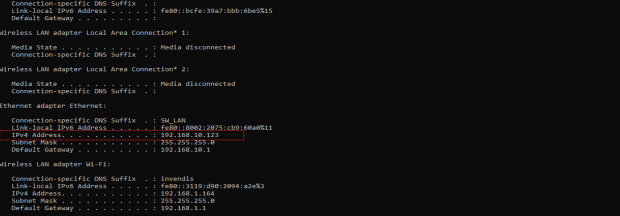
Open the web browser and type the IP address in the URL. | |||
It will show the log in page of the application. | |||
[[File:Log In.png|frameless|620x620px]] | |||
Give the valid credentials for the username and password to login to the application page. | |||
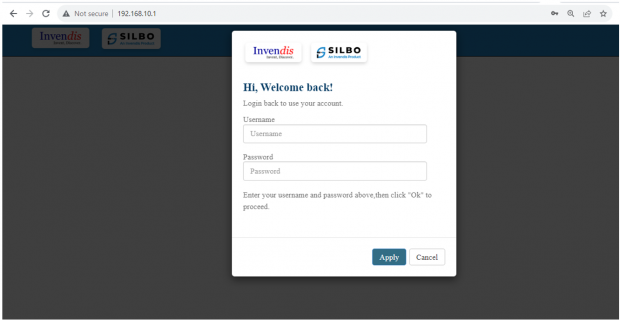
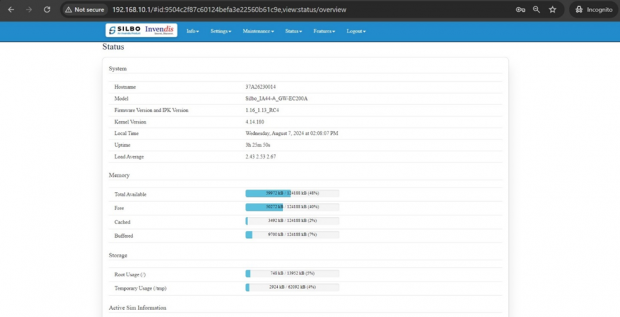
Once the user credentials are provided it will direct to the landing page of the application. | |||
The “Status” landing page shows all the detailed specification of the device like system, memory storage and connection tracking etc. | |||
[[File:IA44A Dashboard.png|frameless|620x620px]] | |||
The application is divided in to 8 Modules. | |||
* Info | |||
* Settings | |||
* Maintenance | |||
* Status | |||
* Features | |||
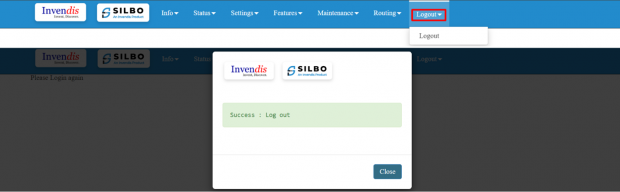
* Logout | |||
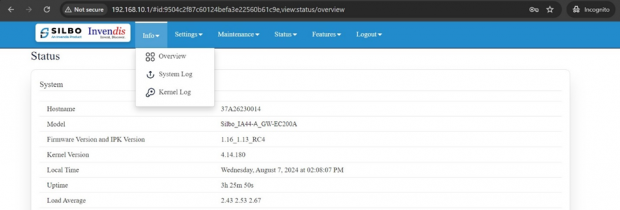
== 1. Info == | |||
The “Info” module provides the information about the devices to the user. | |||
It provides all the specification related to the hardware, firmware, Networks and the Connection uptimes. | |||
It has 3 submodules. | |||
* Overview | |||
* System Log | |||
* Kernel Log | |||
[[File:IA44 A Info.png|frameless|620x620px]] | |||
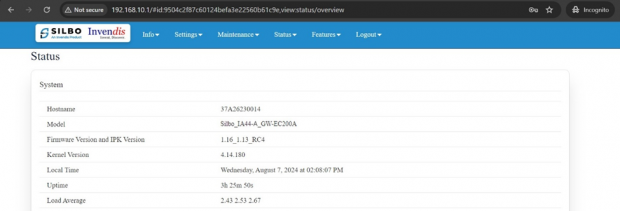
=== 1.1 Overview === | |||
In overview module it displays all the specification categorically of a device like System, Memory, storage, Connection tracking, DHCP Lease. | |||
[[File:IA44A Dashboard.png|frameless|620x620px]] | |||
'''System:''' | |||
In this section it displays the hardware configured specification of the device. | |||
[[File:IA44A Info System Section.png|frameless|620x620px]] | |||
The specifications details are as follows, | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Hostname | |||
|37A26230014 | |||
|This field displays the router serial number of the device | |||
|- | |||
|2 | |||
|Model | |||
|Silbo_IA44-A- EC200A | |||
|This field displays the model number of the device | |||
|- | |||
|3 | |||
|Firmware Version and IPK Version | |||
|1.16_1.13_RC4 | |||
|This field displays the firmware version and IPK version | |||
|- | |||
|4 | |||
|Kernel Version | |||
|4.14.180 | |||
|This field displays the kernel version of the device | |||
|- | |||
|5 | |||
|Local Time | |||
|Monday, July 1, 2024, at 05:43:58 PM | |||
|This field displays the local time | |||
|- | |||
|6 | |||
|Uptime | |||
|0h 7m 29s | |||
|This field displays the uptime of the device | |||
|- | |||
|7 | |||
|Load Average | |||
|1.73 1.87 1.04 | |||
|This field displays the average load | |||
|} | |||
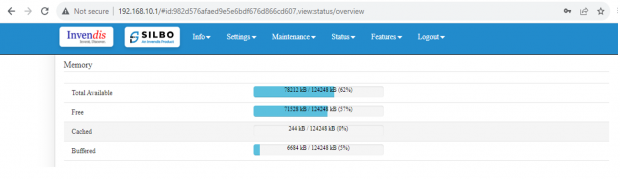
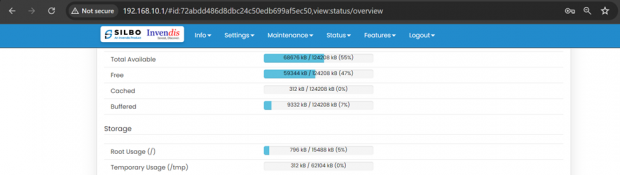
'''Memory:''' | |||
In this section it displays the memory configured specification of the device. | |||
[[File:IA44A Memory.png|frameless|620x620px]] | |||
The specifications details are as follows. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Total Available | |||
|68676 kB / 124208 kB (55%) | |||
|This field displays the total availability of memory space in the device | |||
|- | |||
|2 | |||
|Free | |||
|59344 kB / 124208 kB (47%) | |||
|This field displays the Free memory space in the device | |||
|- | |||
|3 | |||
|Cached | |||
|312 kB / 124208 kB (0%) | |||
|This field displays the Cached memory space in the device | |||
|- | |||
|4 | |||
|Buffered | |||
|9332 kB / 124208 kB (7%) | |||
|This field displays the Buffered memory space in the device | |||
|} | |||
'''Storage:''' | |||
In this section it displays the status of storage as root and temporary usage specification of the device. | |||
[[File:Storage Section.png|frameless|620x620px]] | |||
The specifications details are as follows. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Root Usage | |||
|796 kB / 15488 kB (5%) | |||
|This field displays the total root usage of the device | |||
|- | |||
|2 | |||
|Temporary Usage | |||
|312 kB / 62104 kB (0%) | |||
|This field displays the total temporary usage of the device | |||
|}'''Connection Tracking:''' | |||
In this section it displays the status of connection tracking for the device. | |||
[[File:Connection Tracking.png|frameless|620x620px]] | |||
The specifications details are as follows. | |||
{| class="wikitable" | |||
|SN | |||
|Field Value | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Active Connections | |||
|48/16384 (0%) | |||
|This field displays the active connection of the device. | |||
|} | |||
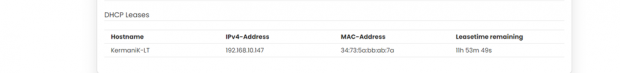
'''DHCP Leases:''' | |||
In this section it displays the DHCP lease of the temporary assignment of an IP address to a device on the network. | |||
[[File:IAB44C DHCP Leases.png|frameless|620x620px]] | |||
The specifications details are below. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Host Name | |||
|KermaniK-LT | |||
|This field displays the configured Host Name/Username for that device. | |||
|- | |||
|2 | |||
|IPv4-Address | |||
|192.168.10.147 | |||
|This field displays the IP address of the device. | |||
|- | |||
|3 | |||
|MAC-Address | |||
|34:73:5a:bb: ab:7a | |||
|This field displays the MAC-Address of the device. | |||
|- | |||
|4 | |||
|Lease time remaining | |||
|11h 53m 49s | |||
|This field displays the lease time remaining for the device. | |||
|} | |||
=== 1.2 System Log === | |||
This page provides on screen System logging information. In this page the user gets to view the system logs.[[File:System Log.png|frameless|620x620px]] | |||
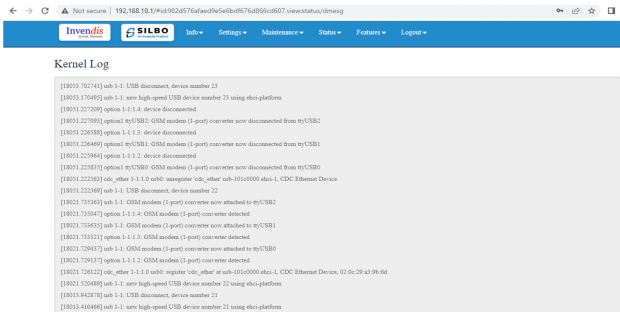
=== 1.3 Kernel Log === | |||
This page provides on screen Kernel logging information. | |||
In this page the user gets to view the Kernel logs. | |||
[[File:Kernel Log.png|frameless|620x620px]] | |||
= 2. Setting = | |||
In this “Setting” module the user can Configure/update all the required parameters related to Network, SIM Switch, Internet, VPN, Firewall, Loopback Rule, Remote monitoring, Tunnel as per requirement. | |||
IT consist of 8 submodules. | |||
* Network | |||
* Sim Switch | |||
* Internet | |||
* VPN | |||
* Firewall | |||
* Loopback Rule | |||
* Remote Monitoring | |||
* Tunnel | |||
[[File:Settings.png|frameless|620x620px]] | |||
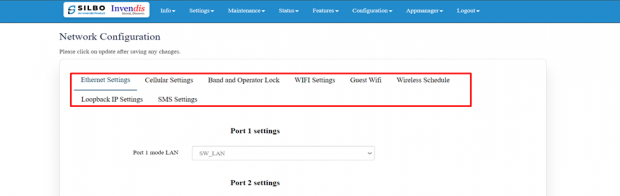
=== 2.1 Network === | |||
In this section the user does all the setting related configuration with reference to network like Ethernet Setting, Cellular Setting, Band lock and Operator Lock, Wi-Fi, Guest Wi-Fi, Wireless Schedule, SMS Setting, Loopback IP. | |||
[[File:IAB44C Network Settings .png|frameless|620x620px]] | |||
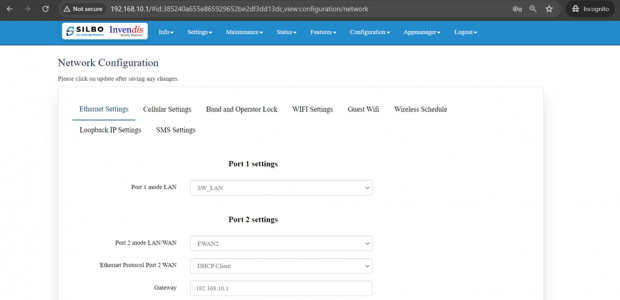
'''Ethernet Setting:''' | |||
In this page it will display all the configured port that is attached with the device. | |||
For this device 2 ports are configured. Ethernet mode can be configured as WAN and as LAN as well. Ethernet LAN Connection settings can be configured as DHCP server or Static. | |||
[[File:IAB44C Ethernet Settings.png|frameless|620x620px]] | |||
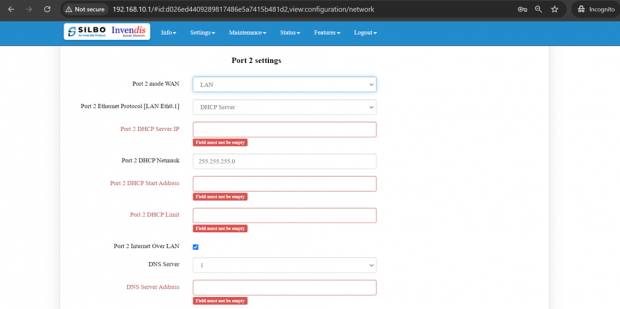
'''For port 2 settings,''' | |||
Kindly select the option '''LAN''' for '''Port 2 mode LAN/WAN'''. Based on the option selected the field will also change. The user needs to configure all the required field and click on the save to save the required fields. | |||
[[File:Port 2 Setting.png|frameless|620x620px]] | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Port 2 mode LAN/WAN | |||
|LAN | |||
|This field displays the port mode selection | |||
|- | |||
|2 | |||
|Port 2 Ethernet Protocol [LAN Eth0.1] | |||
|DHCP Server | |||
|This field displays the Ethernet mode selection | |||
|- | |||
|3 | |||
|Port 2 DHCP Server IP | |||
|192.168.10.1 | |||
|This field displays DHCP server IP configured. | |||
|- | |||
|4 | |||
|Port 2 DHCP Netmask | |||
|255.255.255.0 | |||
|This field displays DHCP server Netmask address configured | |||
|- | |||
|5 | |||
|Port 2 DHCP Start Address | |||
|100 | |||
|This field displays DHCP server start address configured | |||
|- | |||
|6 | |||
|Port 2 DHCP Limit | |||
|50 | |||
|This field displays DHCP server limit | |||
|- | |||
|7 | |||
|Port 2 Internet Over LAN | |||
|Enable | |||
|Enabling this option allows devices connected to Port 2 to access the internet through the LAN. | |||
|- | |||
|8 | |||
|DNS Server | |||
|1/2 | |||
|This setting typically indicates that one or two DNS server is configured. | |||
|- | |||
|9 | |||
|DNS Server Address | |||
|Ex: 8.8.8.8 | |||
|This is the IP address of the DNS server that the devices on your network will use for DNS queries. | |||
|} | |||
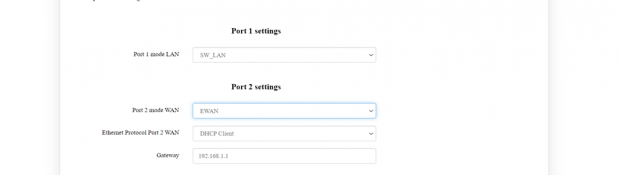
Kindly select the option '''EWAN''' for '''Port 2 mode LAN/WAN'''. Based on the option selected the field will also change. The user needs to configure all the required field and click on the save to save the required fields. | |||
[[File:Port 2 Mode Ewan.png|frameless|620x620px]] | |||
The specifications details are below. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Port 2 mode LAN/WAN | |||
|EWAN | |||
|This field displays the port mode selection | |||
|- | |||
|2 | |||
|Ethernet Protocol Port 2 WAN | |||
|DHCP client | |||
|This field displays the client | |||
|- | |||
|3 | |||
|Gateway | |||
|192.168.1.1 | |||
|This field displays gateway address configured | |||
|} | |||
Click on the save once all the configuration is done and click on the update button to update all the information. | |||
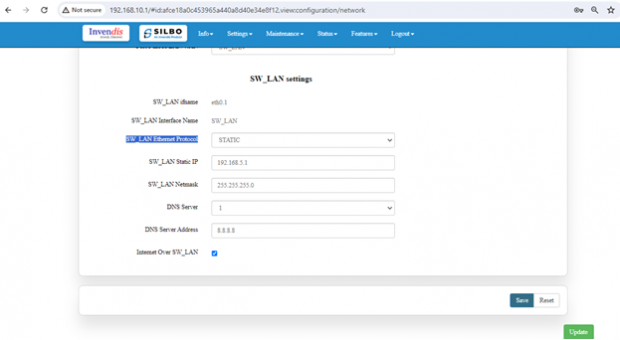
'''SW_LAN settings,''' | |||
In this part the user can configure the setting for SW_LAN. | |||
'''Note:''' After any changes made, save and update the page below. | |||
[[File:SW LAN Settings.png|frameless|620x620px]] | |||
The specifications details are below. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|SW_LAN Ethernet Protocol | |||
|DHCP Server | |||
|This field displays the Ethernet mode selection. | |||
|- | |||
|2 | |||
|SW_LAN DHCP Server IP | |||
|192.168.10.1 | |||
|This field displays DHCP server IP configured which can be changed accordingly. | |||
|- | |||
|3 | |||
|SW_LAN DHCP Netmask | |||
|255.255.255.0 | |||
|This field displays DHCP server Netmask address configured. | |||
|- | |||
|4 | |||
|SW_LAN DHCP Start Address | |||
|100 | |||
|This field displays DHCP server start address configured. | |||
|- | |||
|5 | |||
|SW_LAN DHCP Limit | |||
|50 | |||
|This field displays DHCP server limit. | |||
|- | |||
|6 | |||
|DNS Server | |||
|1 | |||
|This filed display number of DNS server availability. | |||
|- | |||
|7 | |||
|DNS Server Address | |||
|8.8.8.8 | |||
|This filed display the DNS server address. | |||
|} | |||
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information. | |||
'''Static option for SW_LAN Ethernet Protocol:''' | |||
Select the option of static from the drop-down menu for SW_LAN Ethernet Protocol. | |||
'''Note:''' After any changes made, save and update the page below. | |||
[[File:Static option for SW LAN Ethernet Protocol.png|frameless|620x620px]] | |||
The specifications details are below. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|SW_LAN Ethernet Protocol | |||
|Static | |||
|This field displays the Ethernet mode selection | |||
|- | |||
|2 | |||
|SW_LAN static IP | |||
|192.168.5.1 | |||
|This field displays static server IP configured. | |||
|- | |||
|3 | |||
|SW_LAN Netmask | |||
|255.255.255.0 | |||
|This field displays static server Netmask address configured | |||
|- | |||
|4 | |||
|DNS Server | |||
|1 | |||
|This filed display number of DSN server availability | |||
|- | |||
|5 | |||
|DSN Server Address | |||
|8.8.8.8 | |||
|This filed display the DSN server address. | |||
|} | |||
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information. | |||
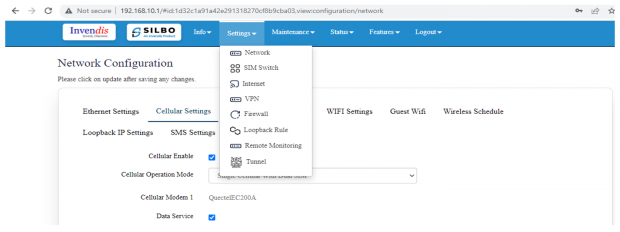
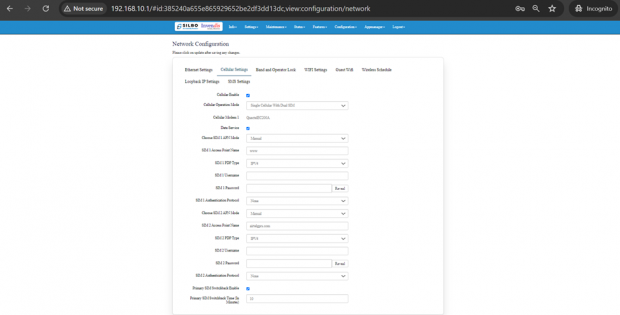
'''Cellular Setting:''' | |||
In this page, the user needs to configure the various details with respect to the SIM. | |||
Select single cellular single sim where the user must configure the APN details of the sim used for the router device. The Configurations can be done based on the SIM usage, with respect to IPV4 or IPV6. | |||
[[File:IAB44C Network Configuration Dashboard.png|frameless|620x620px]] | |||
The specifications details are below. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Cellular Enable | |||
|Checkbox | |||
|Check this box to enable cellular functionality. | |||
|- | |||
|2 | |||
|Cellular Operation Mode | |||
|1.) Single Cellular with Dual Sim | |||
2.) Single Cellular with Single SIM | |||
|1.) This mode allows you to use one cellular modem with two SIM cards. | |||
2.) This mode allows you to use one cellular modem with single SIM card. | |||
|- | |||
|3 | |||
|Cellular Modem 1 | |||
|QuectelEC200A | |||
|This field displays the modem name. | |||
|- | |||
|4 | |||
|Choose SIM 1 APN Mode | |||
|1.) Auto | |||
2.) Manual | |||
|1.) Choose Auto for regular SIM to detect APN name automatically. | |||
2.) Choose manual to enter the APN settings manually in case of M2M SIM cards. | |||
|- | |||
|5 | |||
|SIM 1 Access Point Name | |||
|airtelgprs.com | |||
|Enter the APN provided by your cellular service provider in case of M2M sim. For regular sim cards APN name will be displayed automatically. | |||
|- | |||
|6 | |||
|SIM 1 PDP Type | |||
|IPV4 | |||
|Choose the PDP type, which is typically either IPv4 or IPv6 depending on the sim card. | |||
|- | |||
|7 | |||
|SIM 1 Username | |||
| | |||
|Enter the username if required by the APN. Leave blank if not required. | |||
|- | |||
|8 | |||
|SIM 1 Password | |||
| | |||
|Enter the password if required by the APN. Leave blank if not required. | |||
|- | |||
|9 | |||
|SIM 1 Authentication Protocol | |||
|None | |||
|Choose the authentication protocol. Options typically include None, PAP, or CHAP. | |||
|- | |||
|10 | |||
|Choose SIM 2 APN Mode | |||
|1.) Auto | |||
2.) Manual | |||
|1.) Choose Auto for regular SIM to detect APN name automatically. | |||
2.) Choose manual to enter the APN settings manually in case of M2M SIM cards. | |||
|- | |||
|11 | |||
|SIM 2 Access Point Name | |||
|airtelgprs.com | |||
|Enter the APN provided by your cellular service provider in case of M2M sim. For regular sim cards APN name will be displayed automatically. | |||
|- | |||
|12 | |||
|SIM 2 PDP Type | |||
|IPV4 | |||
|Choose the PDP type, which is typically either IPv4 or IPv6 depending on the sim card. | |||
|- | |||
|13 | |||
|SIM 2 Username | |||
| | |||
|Enter the username if required by the APN. Leave blank if not required. | |||
|- | |||
|14 | |||
|SIM 2 Password | |||
| | |||
|Enter the password if required by the APN. Leave blank if not required. | |||
|- | |||
|15 | |||
|SIM 2 Authentication Protocol | |||
|None | |||
|Choose the authentication protocol. Options typically include None, PAP, or CHAP. | |||
|- | |||
|16 | |||
|Primary SIM Switchback Time (In Minutes) | |||
|10 | |||
|Enter the time in minutes after which the system should switch back to the primary SIM if it becomes available. | |||
|} | |||
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information. | |||
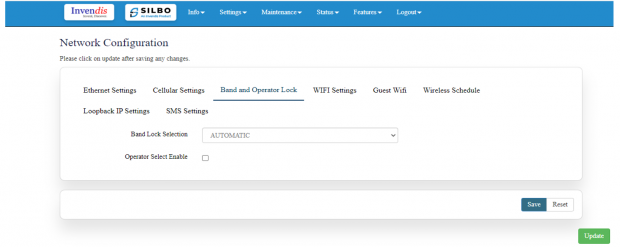
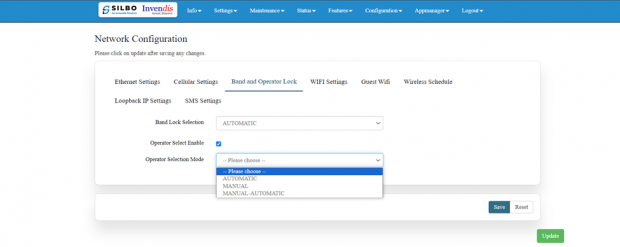
'''Band lock and Operator Lock:''' | |||
In this page, the user needs to configure the lock band and operator based on the service provider'''.''' | |||
Bands available in the drop-down list. | |||
[[File:Band lock and Operator Lock.png|frameless|620x620px]] | |||
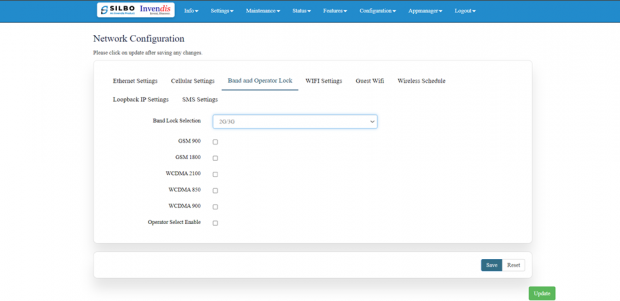
'''2G/3G option:''' | |||
2G/3G: - 3G allows additional features such as mobile internet access, video calls and mobile TV. While the main function of 2G technology is the transmission of information through voice calls. | |||
[[File:Band and Operator Lock settings Dashboard.png|frameless|620x620px]] | |||
The user should select the band check box available for 2g/3g from the given list. Bands available for selection under LTE for the bands available in that area. | |||
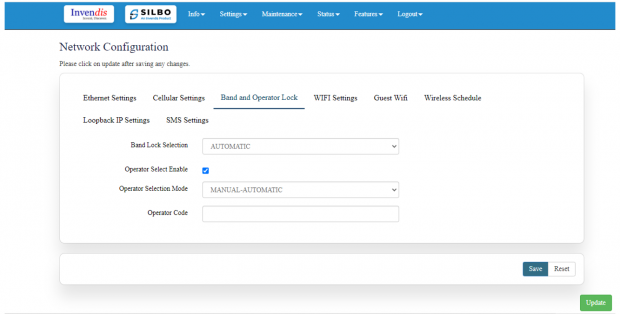
'''Operator Selection Mode:''' | |||
The user needs to click on the check box of the “operator select enable” to select the operator. | |||
Once the check box is clicked there will be a dropdown list of the operator modes from which the user needs to select the mode. The user needs to select the operator mode from the given dropdown list. | |||
[[File:Band and Operator Lock settings 2.png|frameless|620x620px]] | |||
If the user selects the mode “Manual” or “Manual-Automatic” then one more text box will appear where the user must provide the operator code. | |||
[[File:Band lock and Operator Lock 1.png|frameless|620x620px]] | |||
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information. | |||
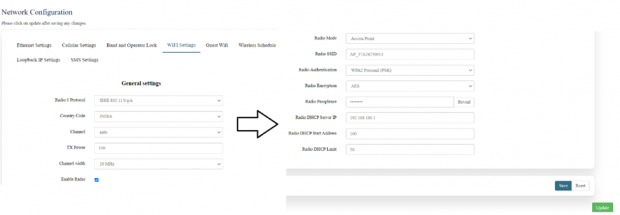
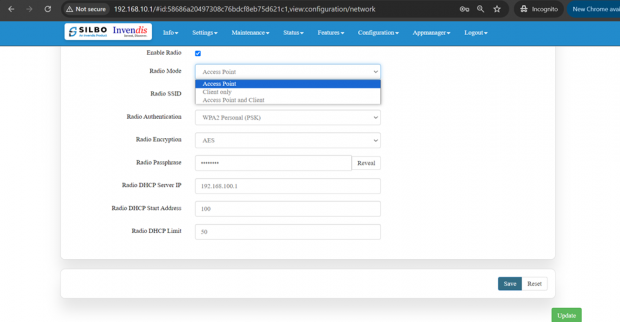
'''Wi-Fi Setting:''' | |||
In this, router has the general setting and change country code, channel, radio mode, radio passphrase as per the requirement after clicking on enable Radio button. | |||
The user needs to select the respective radio mode based on its need. | |||
[[File:Wifi General Settings .png|frameless|620x620px]] | |||
It has 3 radio modes. | |||
‘Access point’, ‘client only’ and ‘Access point and client’ | |||
Refer the below picture. | |||
[[File:Access point update.png|frameless|620x620px]] | |||
'''Access Point mode:''' | |||
In Access Point mode, a configuration in which a router, allows wireless devices to connect to a wired network by creating a Wi-Fi hotspot. | |||
[[File:Access point update.png|frameless|620x620px]] | |||
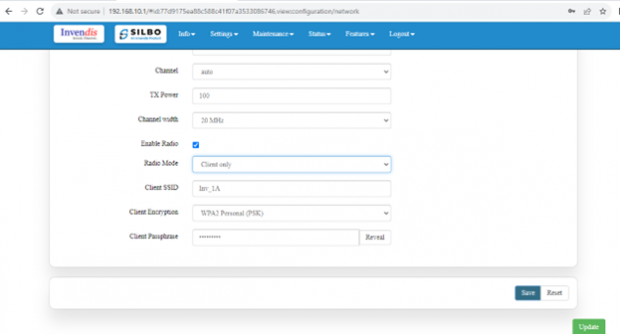
'''Client point:''' | |||
In client mode, the access point connects your wired devices to a wireless network. This mode is suitable when you have a wired device with an Ethernet port and no wireless capability, for example, a smart TV, Media Player, or Game console and you want to connect it to the internet wirelessly, select the Client Mode and give the Radio SSID & client passphrase. | |||
[[File:Client point.png|frameless|620x620px]] | |||
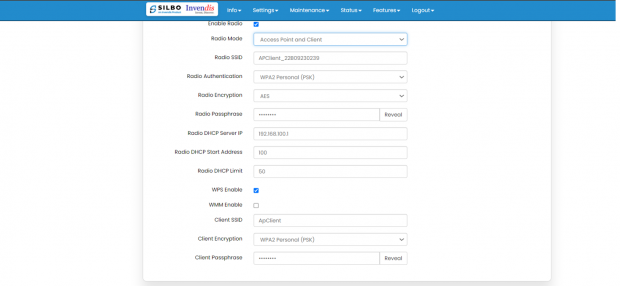
'''Access point and client point''': | |||
Select this option for both type of connection, give both SSID and passphrase. | |||
[[File:Access point and Client Point RC44.png|frameless|620x620px]] | |||
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information. | |||
The specifications details are below. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Radio 0 Protocol | |||
|IEEE 802.11 b/g/n | |||
|This section shows the radio protocol which is by default. | |||
|- | |||
|2 | |||
|Country Code | |||
|INDIA | |||
|Select the country accordingly. | |||
(INDIA by default) | |||
|- | |||
|3 | |||
|Channel | |||
|Auto | |||
|In this dropdown the user should select the proper channel to be used. (Auto by default) | |||
|- | |||
|4 | |||
|TX Power | |||
|100 | |||
|In this text box the user should specify the power. | |||
|- | |||
|5 | |||
|Channel Width | |||
|20 MHz | |||
|In this dropdown the user should select the channel width | |||
|- | |||
|6 | |||
|Radio Mode | |||
|1.) Access point | |||
2.) Client only | |||
3.) Access point and client | |||
|In this drop down the user should select the mode. | |||
(Access point by default) | |||
|- | |||
|7 | |||
|Radio SSID | |||
|AP_37A26230014 | |||
|In this text box the user should specify the SSID number which usually comes with the router. | |||
|- | |||
|8 | |||
|Radio Authentication | |||
|WPA2 Personal (PSK) | |||
|In this dropdown the user should select the type of authentication. | |||
(WPA2 Personal (PSK) by default) | |||
|- | |||
|9 | |||
|Radio Encryption | |||
|AES | |||
|In this dropdown the user should select the type of encryption required. | |||
(AES by default) | |||
|- | |||
|10 | |||
|Radio Passphrase | |||
|********* | |||
|In this text box the user should specify the password. Password will be given with the router which can be changed later. | |||
|- | |||
|11 | |||
|Radio DHCP server IP | |||
|192.168.100.1 | |||
|In this text box the user should specify the IP address of DHCP server. | |||
(192.168.100.1 will be default which can be changed accordingly) | |||
|- | |||
|12 | |||
|Radio DHCP start address | |||
|100 | |||
|In this text box the user should specify the start address of the DHCP. | |||
(100 value is default) | |||
|- | |||
|13 | |||
|Radio DHCP limit | |||
|50 | |||
|In this text box the user should specify the limit for the DHCP. | |||
(50 value is default) | |||
|} | |||
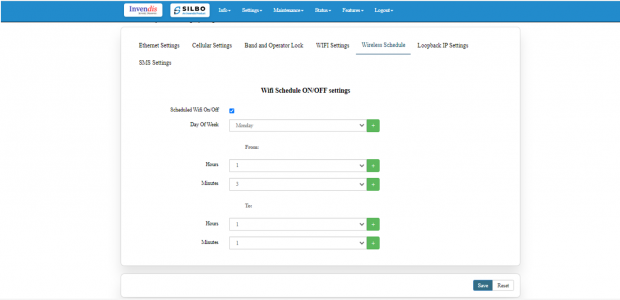
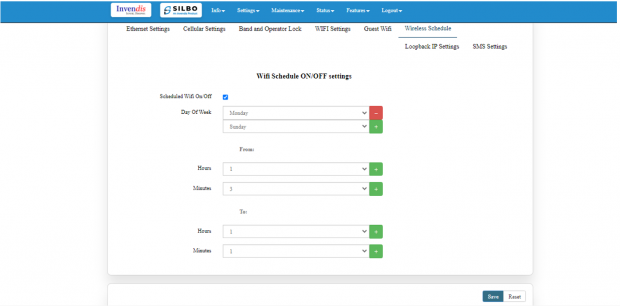
'''Wireless Schedule:''' | |||
Wi-Fi can be automatically withdrawn based on the configuration done in this section. | |||
The user can schedule the Wi-Fi’s accessibility time during a particular period. | |||
[[File:Wireless Schedule.png|frameless|620x620px]] | |||
After configuring all the required information, the user should click on save and then click on update to update all the required information. | |||
The user can select more than one “day of the week” for scheduling the Wi-Fi working hours. | |||
[[File:Wifi Schedule.png|frameless|620x620px]] | |||
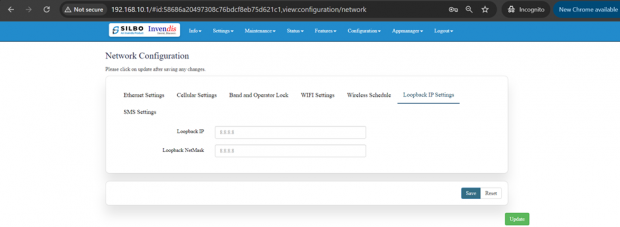
'''Loop back IP settings:''' | |||
The loopback IP address, often referred to as “localhost.” it is used to establish network connections within the same device for testing and troubleshooting purpose. | |||
The loopback IP address, commonly represented as 127.0.0.1, is a special address used for testing network connectivity on a local machine. | |||
It allows a device to send network messages to itself without involving external networks, making it useful for troubleshooting and diagnostics. | |||
However, this IP can be changed as per requirement and to do that, Navigating to Setting>>Network configuration>> Loopback IP settings can be changed/updated. | |||
[[File:Loopback Update.png|frameless|620x620px]] | |||
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information. | |||
The loopback IP address, commonly represented as 127.0.0.1, is a special address used for testing network connectivity on a local machine. It allows a device to send network messages to itself without involving external networks, making it useful for troubleshooting and diagnostics. | |||
However, this IP can be changed as per requirement and to do that, Navigating to Setting>>Network configuration>> Loopback IP settings can be changed/updated. | |||
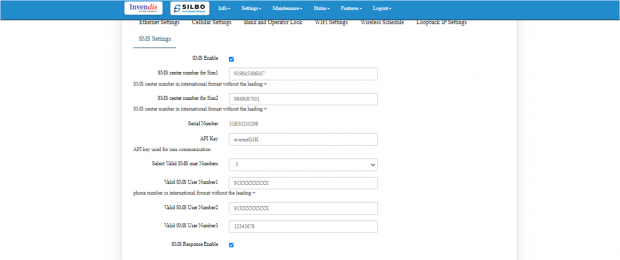
'''SMS Settings:''' | |||
User needs to enable SMS option in SMS settings page. | |||
This option is to validate the mobile numbers using which controlling commands could be sent to the router device. | |||
1 to 5 mobile numbers can be authenticated by choosing from “Select Valid SMS user numbers” and adding the mobile numbers below respectively. | |||
API key is the pass key used in the commands while sending SMS. | |||
Displayed in the below screen is the default API key which can be edited and changed as per choice. After addition of the mobile number’s user needs to click on save button for changes to take place. | |||
[[File:SMS Settings.png|frameless|620x620px]] | |||
1.) Select valid user number max. 5 and add authorized phone number in the tab where you want to find the alert and click on '''‘SMS Response Enable’''', '''‘save’''' and '''‘update’''' button. | |||
2.) Now send SMS commands from the configured mobile number. | |||
3.) Once the commands are received from the user phone number the board will send acknowledgement as per the commands. | |||
4.) After that it will send the router’s status once it has rebooted and is operational again. | |||
Mentioned below are a few commands which can be sent from the configured mobile number to the router device. Below two commands are One for rebooting the router device and another to get the uptime. | |||
1) {"device”: ["passkey”, “API key"],"command":"reboot","arguments":"hardware"} | |||
2) {"device”: ["passkey ","API key"],"command”: “uptime"} | |||
After configuring all the required information, the user should click on save and then click on update to update all the required information. | |||
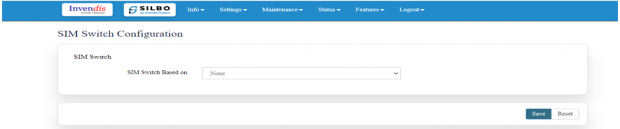
=== 2.2 SIM Switch === | |||
In this page the user needs to configure the Sim for the given device. | |||
[[File:SIM Switch.png|frameless|620x620px]] | |||
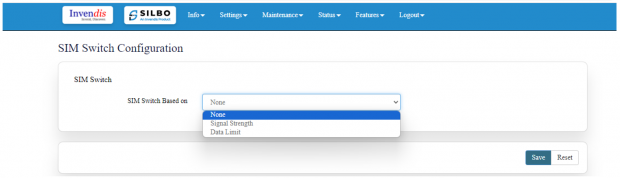
The user needs to select from the drop-down menu on which basis the sim needs to be switched. | |||
[[File:Sim Switch Configuration.png|frameless|620x620px]] | |||
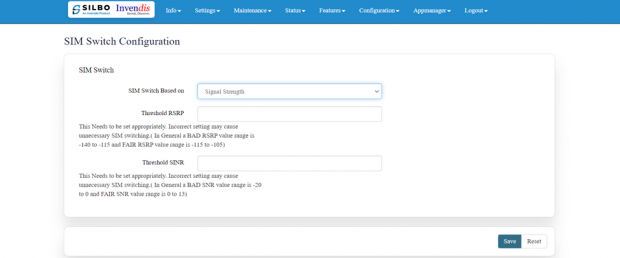
Once the user selects on “'''signal strength'''” then the parameters related to signal strength will pop up and the user needs to configure the parameters based on the requirement. | |||
[[File:SIM Switch Configuration.png|frameless|620x620px]] | |||
'''Threshold RSRP:''' | |||
This Needs to be set appropriately. Incorrect setting may cause unnecessary SIM switching. (In General, a BAD RSRP value range is -140 to -115 and FAIR RSRP value range is -115 to -105). | |||
'''Threshold SINR:''' | |||
This Needs to be set appropriately. Incorrect setting may cause unnecessary SIM switching. (In General, a BAD SNR value range is -20 to 0 and FAIR SNR value range is 0 to 13) | |||
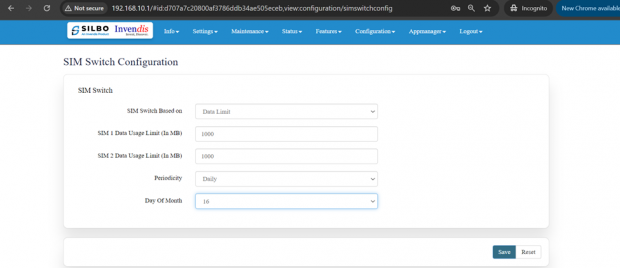
Once the user selects on “'''Data Limit'''” then the parameters related to Data Limit will pop up and the user needs to configure the parameters based on the requirement. | |||
[[File:Threshold SINR.png|frameless|620x620px]] | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|SIM Switch Based on | |||
|Data Limit | |||
|The user needs to select from the drop-down menu on what basis the sim needs to be switched. | |||
|- | |||
|2 | |||
|SIM 1 Data Usage Limit (In MB) | |||
|1000 | |||
|The user needs to set the limit for the data usage for SIM 1. | |||
|- | |||
|3 | |||
|SIM 2 Data Usage Limit (In MB) | |||
|1000 | |||
|The user needs to set the limit for the data usage for SIM 2. | |||
|- | |||
|4 | |||
|Periodicity | |||
|Daily | |||
|The user needs to set the pattern/frequency to switch the sims. | |||
|- | |||
|5 | |||
|Day Of Month | |||
|16 | |||
|The user needs to set the day for switching the sim. | |||
|} | |||
=== 2.3 Internet === | |||
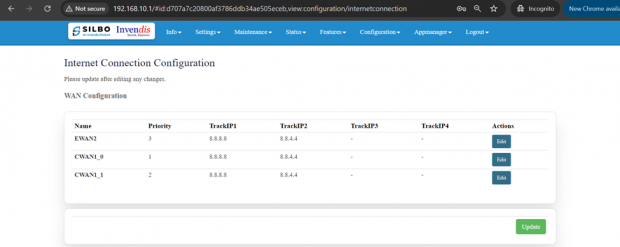
In this page the user needs to configure the internet connection to set the priority from the diverse options. The user should decide what kind of connection it needs to provide to the device like LAN, WAN etc. Once the connections are configured then click on save option and then on update. | |||
[[File:Internet Connection Configurtion.png|frameless|620x620px]] | |||
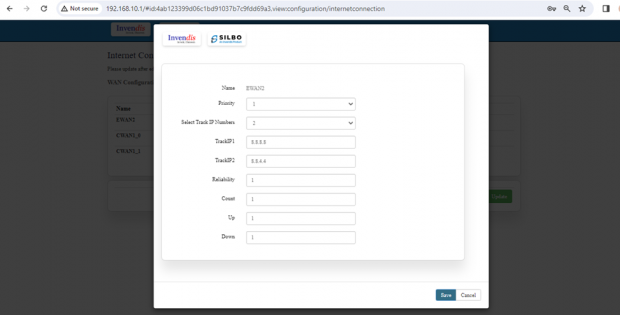
If the user needs to edit on the existing configuration, then the user should click on the “EDIT” button. | |||
[[File:EWAN2 Edit Options.png|frameless|620x620px]] | |||
The specifications details are below. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Name | |||
|EWAN2 | |||
|This field displays the name of the WAN connection | |||
|- | |||
|2 | |||
|Priority | |||
|1 | |||
|In this dropdown box the user needs to select the priority. | |||
|- | |||
|3 | |||
|Select Track IP Numbers | |||
|2 | |||
|In this dropdown the user needs to select the track number for the Ips. This specifies the number of IP addresses that will be used for tracking the status of the connection. | |||
|- | |||
|4 | |||
|TrackIP1 | |||
|8.8.8.8 | |||
|This is the first IP address used for tracking the connection. <code>8.8.8.8</code> is a public DNS server provided by Google. | |||
|- | |||
|5 | |||
|TrackIP2 | |||
|8.8.4.4 | |||
|This is the second IP address used for tracking the connection. <code>8.8.4.4</code> is another public DNS server provided by Google. | |||
|- | |||
|6 | |||
|Reliability | |||
|1 | |||
|This indicates the reliability threshold for considering the connection as up. A value of <code>1</code> typically means that only one successful ping response is needed to deem the connection reliable. | |||
|- | |||
|7 | |||
|Count | |||
|1 | |||
|This specifies the number of consecutive pings sent to the track IP addresses. | |||
|- | |||
|8 | |||
|Up | |||
|1 | |||
|This indicates the number of successful pings required to consider the connection as up. | |||
|- | |||
|9 | |||
|Down | |||
|1 | |||
|This indicates the number of failed pings required to consider the connection as down. | |||
|} | |||
Once the user is done with modification click on the save button to save all the changes and then click on the update button. | |||
=== 2.4 VPN === | |||
VPN stands for '''Virtual Private Network''', it establishes a connection between the system and a remote server, which is owned by a VPN provider. | |||
Creating a point-to-point tunnel that encrypts the personal data, masks the IP address, and allows to block the required website to blocks via firewalls on the internet. | |||
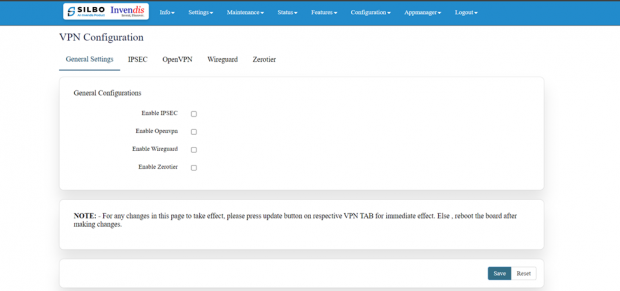
Navigate to settings >= VPN, general settings and you will see all VPN options you wish to use. | |||
Refer the below figure. | |||
[[File:VPN Configuration General Settings.png|frameless|620x620px]] | |||
There are 5 types of setting available under VPN configuration. | |||
* General Settings | |||
* IPSEC | |||
* Open VPN | |||
* Wireguard | |||
* Zerotier | |||
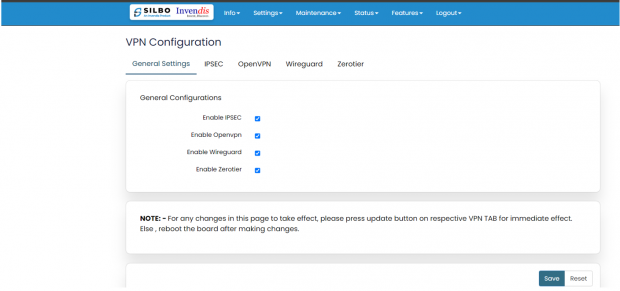
'''General Settings:''' | |||
In this page the user must choose which type of VPN connection is required for the device. The user must select from IPSEC, Open VPN, Wireguard or Zerotier based on its requirement. If required, the user can select all the options. The user needs to click on the save after selecting the option based on its use. | |||
[[File:VPN General Settings RC44.png|frameless|620x620px]] | |||
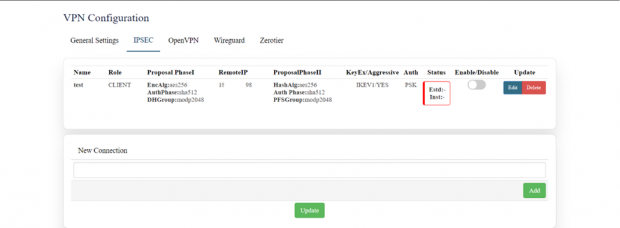
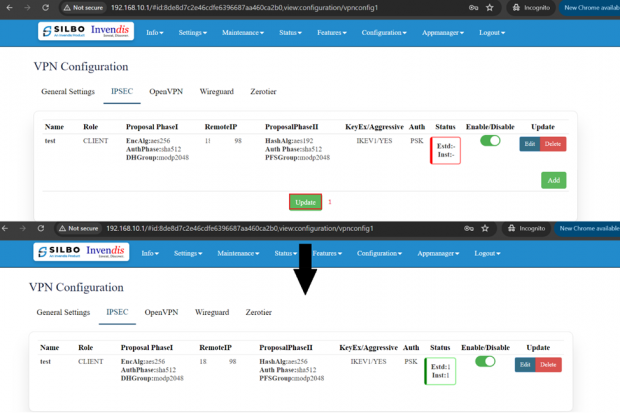
'''IPSEC:''' | |||
IPSEC VPN is used to create a VPN connection between local and remote networks. | |||
To use IPSEC VPN, the user should check that both local and remote routers support IPSEC VPN feature. | |||
In this page the user can add/edit/delete the IPSEC VPN connection for the device. | |||
[[File:IAB44C Ipsec VPN Dashboard.png|frameless|620x620px]] | |||
The user needs to click on the update button once the required configuration is completed. | |||
In IPSEC the user needs to click on edit button to edit the configuration of an existing VPN connection. | |||
[[File:IAB44C Ipsec Edit Options.png|frameless|620x620px]] | |||
Click on update once done with configurations. | |||
The tunnel will show established, showing the connection has been made. | |||
[[File:VPN Configurtaion IPSEC .png|frameless|620x620px]] | |||
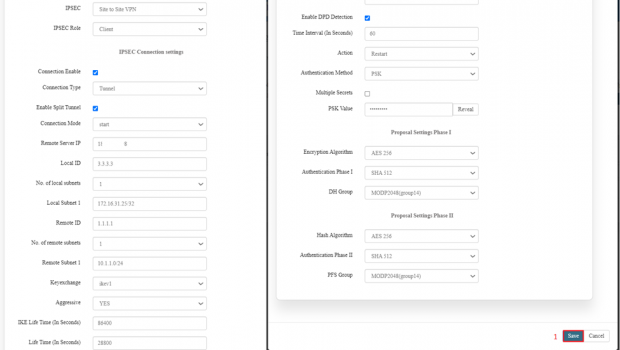
Detailed specifications are below: | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|IPSEC | |||
|Site to Site VPN | |||
|In this dropdown the user should select the IPSEC connection type. | |||
|- | |||
|2 | |||
|IPSEC Role | |||
|Client/Server | |||
|In this dropdown box the user needs to select the IPSEC role. The device is acting as a client in the VPN setup (in this example). | |||
|- | |||
|3 | |||
|Connection Type | |||
|Tunnel | |||
|In this dropdown the user needs to select the connection type. The user should select on the connection enable check box. | |||
|- | |||
|4 | |||
|Connection mode | |||
|Route/add/'''start'''/trap | |||
|In this drop down list the user should select the mode for the connection. In this example '''start''' is selected which means the VPN connection is initiated automatically. | |||
|- | |||
|5 | |||
|Remote Server IP | |||
|******** | |||
|The IP address of the remote VPN server. | |||
|- | |||
|6 | |||
|Local ID | |||
|3.3.3.3 | |||
|The user needs to set the local id. It is the identification for the local VPN client. | |||
|- | |||
|7 | |||
|No. of local subnets | |||
|1 | |||
|In this dropdown the user needs to select how many subnets will be connected. | |||
|- | |||
|8 | |||
|Local Subnet 1 | |||
|172.16.31.25/32 | |||
|In this text box the user needs to put the specific local subnet included in the VPN. | |||
|- | |||
|9 | |||
|Remote id | |||
|1.1.1.1 | |||
|In this text box the user needs to put the id of the remote connection. It is the identification for the remote VPN server. | |||
|- | |||
|10 | |||
|No of remote subnet | |||
|1 | |||
|In this dropdown the user needs to select how many subnets it will be connected remotely. | |||
|- | |||
|11 | |||
|Remote subnet | |||
|10.1.1.0/24 | |||
|In this text box the user needs to put the address of the remote subnet. The specific remote subnet included in the VPN. | |||
|- | |||
|12 | |||
|Key exchange | |||
|Ikev1 | |||
|In this dropdown the user should select the which key exchange version to be selected. | |||
|- | |||
|13 | |||
|Aggressive | |||
|Yes/No | |||
|In this dropdown the user should select either yes or no. | |||
|- | |||
|14 | |||
|IKE Lifetime (In Seconds) | |||
|86400 | |||
|The lifetime of the IKE phase in seconds (1 day). | |||
|- | |||
|15 | |||
|Lifetime (in seconds) | |||
|28800 | |||
|The lifetime of the IPsec SA (Security Association) in seconds (8 hours). | |||
|- | |||
|16 | |||
|Enable DPD Detection | |||
|'''1''' | |||
0 | |||
|Indicates whether Dead Peer Detection is enabled to detect a lost connection. Enable this option as per server-side settings. | |||
|- | |||
|17 | |||
|Time Interval (In Seconds) | |||
|60 | |||
|This option is available only if DPD Detection is enabled. The time interval is the interval for DPD checks. | |||
|- | |||
|18 | |||
|Action | |||
|'''Restart'''/clear/hold/ | |||
trap/start | |||
|'''Restart''': Action to take when DPD detects a lost connection (restart the connection). Select as per server-side setting. | |||
|- | |||
|19 | |||
|Authentication Method | |||
|'''PSK''' | |||
|'''PSK''': Pre-shared key is used for authentication. Select this option for authentication as per sever side setting. | |||
|- | |||
|20 | |||
|Multiple Secrets | |||
|1/'''0''' | |||
|Indicates whether multiple PSK secrets are used. Enable only if required. | |||
|- | |||
|21 | |||
|PSK Value | |||
|****** | |||
|Pre-shared key value (masked for security). | |||
|} | |||
{| class="wikitable" | |||
| colspan="7" |'''Proposal settings Phase I''' | |||
|- | |||
|22 | |||
| colspan="2" |'''Encryption Algorithm''' | |||
| colspan="3" |AES 128 | |||
AES 192 | |||
'''AES 256''' | |||
3DES | |||
|'''AES 256''': Encryption algorithm for Phase I. Select as per server-side configuration. Both server and client should have same configuration. | |||
|- | |||
|23 | |||
| colspan="2" |Authentication Phase I | |||
| colspan="3" |SHA1 | |||
MD5 | |||
SHA 256 | |||
SHA 384 | |||
'''SHA 512''' | |||
|'''SHA 512''': Authentication algorithm for Phase I. | |||
Select as per server-side configuration. Both server and client should have same configuration. | |||
|- | |||
|24 | |||
| colspan="2" |DH Group | |||
| colspan="3" |MODP768(group1) | |||
MODP1024(group2) | |||
MODP1536(group5) | |||
'''MODP2048(group14)''' | |||
MODP3072(group15) | |||
MODP4096(group16) | |||
|'''MODP2048 (group14)''': Diffie-Hellman group for key exchange. | |||
Select as per server-side configuration. Both server and client should have same configuration. | |||
|- | |||
| colspan="7" |'''Proposal settings Phase II''' | |||
|- | |||
| colspan="2" |25 | |||
| colspan="2" |Hash Algorithm | |||
|AES 128 | |||
AES 192 | |||
'''AES 256''' | |||
3DES | |||
| colspan="2" |'''AES 256''': Encryption algorithm for Phase II. Select as per server-side configuration. Both server and client should have same configuration. | |||
|- | |||
| colspan="2" |26 | |||
| colspan="2" |Authentication Phase II | |||
|SHA1 | |||
MD5 | |||
SHA 256 | |||
SHA 384 | |||
'''SHA 512''' | |||
| colspan="2" |'''SHA 512''': Authentication algorithm for Phase II. | |||
Select as per server-side configuration. Both server and client should have same configuration. | |||
|- | |||
| colspan="2" |27 | |||
| colspan="2" |PFS Group | |||
|MODP768(group1) | |||
MODP1024(group2) | |||
MODP1536(group5) | |||
'''MODP2048(group14)''' | |||
MODP3072(group15) | |||
MODP4096(group16) | |||
| colspan="2" |'''MODP2048 (group14)''': Perfect Forward Secrecy group. | |||
Select as per server-side configuration. Both server and client should have same configuration. | |||
|}'''Open VPN:''' | |||
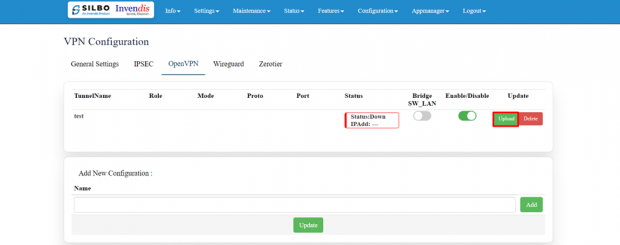
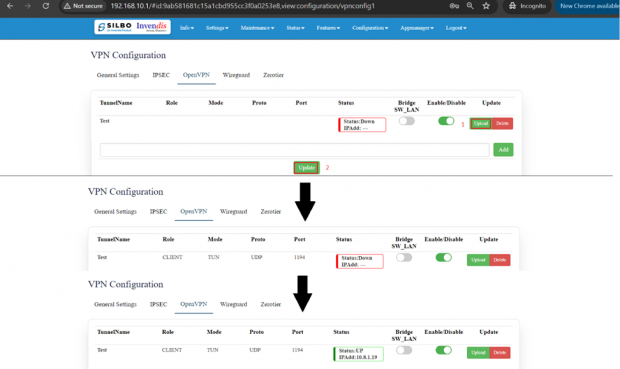
In the OpenVPN connection, the home network can function as a server, and the remote device can access the server through the router which acts as an OpenVPN Server gateway. | |||
To use the VPN feature, the user should enable OpenVPN Server on the router, and install and run VPN client software on the remote device. | |||
[[File:Open VPN Settings .png|frameless|620x620px]] | |||
The user needs to “upload” the respective certificate from a valid path and then click on the “Update.” | |||
Once the OpenVPN connection starts the user will get an option to enable/disable the VPN connection as and when required. | |||
By clicking on the enable/disable button, the user can start/stop the VPN connection. | |||
[[File:Open VPN Dashboard.png|frameless|620x620px]] | |||
VPN has been established. | |||
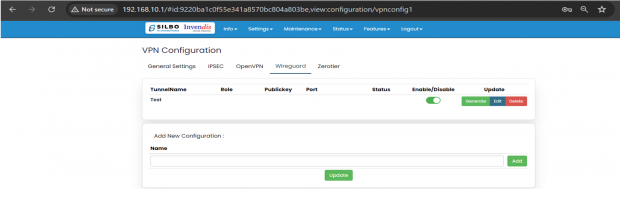
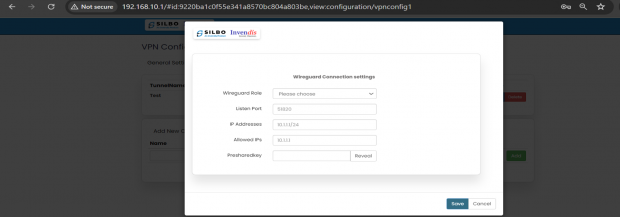
'''WireGuard:''' | |||
'''WireGuard''' is simple, fast, lean, and modern VPN that utilizes secure and trusted cryptography. | |||
Click on “Edit” to start configurations as needed. | |||
[[File:Wire Guard RC44.png|frameless|620x620px]] | |||
EDIT: | |||
[[File:Wire Guard RC44 Setttings.png|frameless|620x620px]] | |||
Click on the save button after the required configuration. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Wireguard Role | |||
|Client/Server | |||
|In this dropdown box the user needs to select the wireguard role. | |||
|- | |||
|2 | |||
|Listen Port | |||
|51820 | |||
|The UDP port on which the WireGuard client listens for incoming connections. | |||
|- | |||
|3 | |||
|IP Addresses | |||
|10.0.0.1/24 | |||
|The IP address and subnet mask assigned to the WireGuard client's interface. This address is used within the VPN. | |||
|- | |||
|4 | |||
|Allowed PeerIPs | |||
|10.1.1.1 | |||
|The IP address of the allowed peer(s) that can connect to this WireGuard client. This might need adjustment based on the actual peer IPs used in the network. | |||
|- | |||
|5 | |||
|Endpoint HostIP | |||
|10.1.1.1 | |||
|The IP address of the WireGuard server (the endpoint to which the client connects). | |||
|- | |||
|6 | |||
|Endpoint HostPort | |||
|51820 | |||
|The port on the WireGuard server to which the client connects. | |||
|- | |||
|7 | |||
|PeerPublicKey | |||
|***** | |||
|The public key of the peer (the server) the client is connecting to. This key is part of the public-private key pair used in WireGuard for encryption and authentication. | |||
|- | |||
|8 | |||
|Enable Preshared key | |||
|Yes/No | |||
|This option indicates that a pre-shared key (PSK) is used in addition to the public-private key pair for an extra layer of security. | |||
|- | |||
|9 | |||
|Preshared key | |||
|***** | |||
|The actual pre-shared key value shared between the client and the server. This option appears only if you have enabled preshared key. | |||
|} | |||
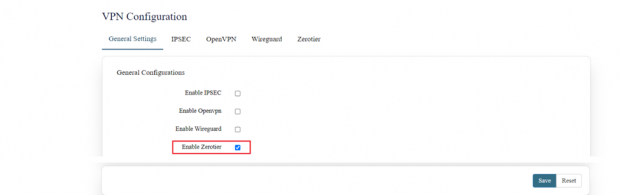
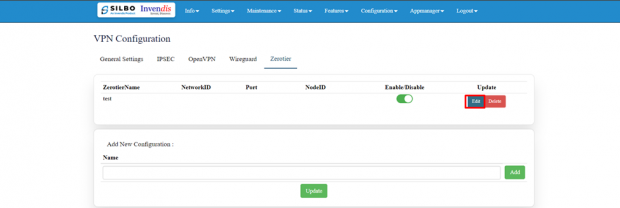
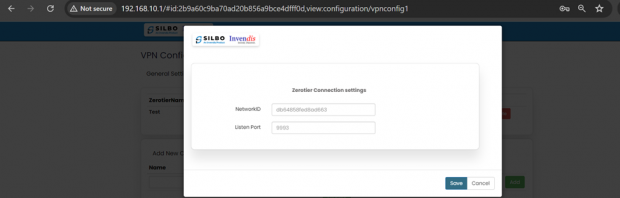
'''Zerotier:''' | |||
ZeroTier is a tool that lets you create your own private network over the internet. | |||
Go to ZeroTier Central and sign up for a free account. In ZeroTier Central, click on "Create a Network". This will generate a unique 16-digit network ID for your new network. | |||
Go to settings => VPN, in general settings, enable ZeroTier and save. | |||
[[File:Zero Tier Enabling.png|frameless|620x620px]] | |||
Copy and paste the unique 16-digit network ID in the edit section. | |||
[[File:Zero tier Unique ID.png|frameless|620x620px]] | |||
[[File:Zerotier Connection.png|frameless|620x620px]] | |||
Click on the save button after the required configuration. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|NetworkID | |||
|Ad2769hfkw2345f4 | |||
|In this dropdown box the user needs to paste the unique 16-digit network id. | |||
|- | |||
|2 | |||
|Listen Port | |||
|9993 | |||
|Default | |||
|} | |||
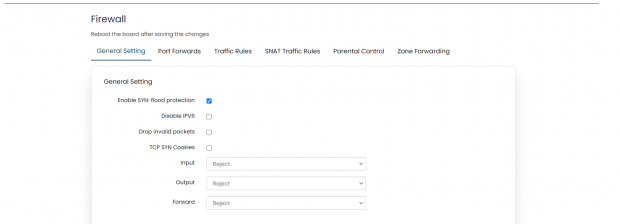
=== 2.5 Firewall === | |||
A firewall is a layer of security between the network and the Internet. Since a router is the main connection from a network to the Internet, the firewall function is merged into this device. Every network should have a firewall to protect its privacy. | |||
[[File:Firewall General Settings.png|frameless|620x620px]] | |||
There are 6 types of setting available under firewall. | |||
* General Settings | |||
* Port forwards | |||
* Traffic Rules | |||
* SNAT traffic Rules | |||
* Parental Control | |||
* Zone Forwarding | |||
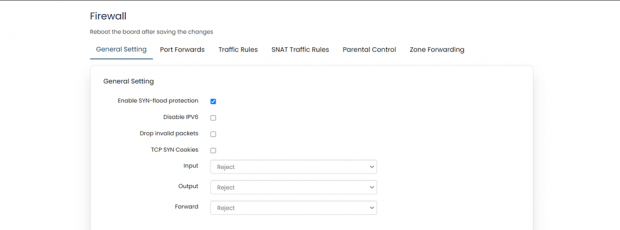
'''General Settings:''' | |||
General settings are subdivided into 2 parts, | |||
1.) General settings | |||
In general settings, the settings that are made are default settings and can be changed according to user’s preference. | |||
[[File:Firewall Configuration 1.png|frameless|620x620px]] | |||
{| class="wikitable" | |||
|'''SN''' | |||
|'''Field Name''' | |||
|'''Sample Value''' | |||
|'''Description''' | |||
|- | |||
|1 | |||
|Enable SYN-flood protection | |||
|Enabled | |||
|This is enabled by default; setting can be changed if required. | |||
|- | |||
|2 | |||
|Disable IPV6 | |||
|Disabled | |||
|This is enabled by default; setting can be changed if required. | |||
|- | |||
|3 | |||
|Drop invalid packets | |||
|Disabled | |||
|This is enabled by default; setting can be changed if required. | |||
|- | |||
|4 | |||
|TCP SYN Cookies | |||
|Disabled | |||
|This is enabled by default; setting can be changed if required. | |||
|- | |||
|5 | |||
|Input | |||
|Reject/Accept | |||
|By default, the setting is ‘Reject’ but this needs to be changed to ‘Accept’ compulsory. | |||
|- | |||
|6 | |||
|Output | |||
|Reject/Accept | |||
|By default, the setting is ‘Reject’ but this needs to be changed to ‘Accept’ compulsory. | |||
|- | |||
|7 | |||
|Forward | |||
|Reject/Accept | |||
|By default, the setting is ‘Reject’ but this needs to be changed to ‘Accept’ compulsory. | |||
|} | |||
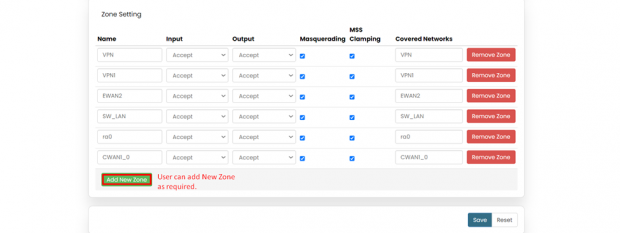
2.) Zone settings | |||
In zone settings, there’s an option to add “New Zone”, according to user’s requirement. | |||
[[File:Firewall Zone Settings.png|frameless|620x620px]] | |||
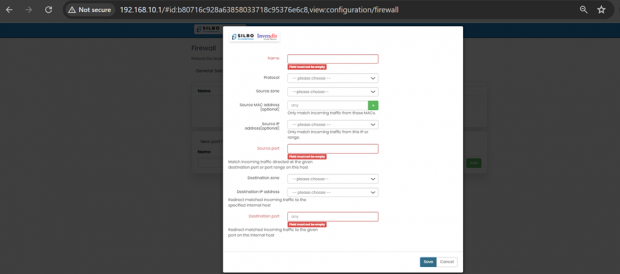
'''Port Forwards:''' | |||
Port forwarding is a feature in a router or gateway that allows external devices to access services on a private network. | |||
It maps an external port on the router to an internal IP address and port on the local network, enabling applications such as gaming servers, web servers, or remote desktop connections to be accessed from outside the network. | |||
This helps in directing incoming traffic to the correct device within a local network based on the port number, enhancing connectivity and accessibility. | |||
[[File:Firewall Enabled.png|frameless|620x620px]] | |||
EDIT: | |||
[[File:Firewall Configuration 2.png|frameless|620x620px]] | |||
Click on the save button after the required configuration. | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Name | |||
|Example: <code>Web_Server_Forward</code> | |||
|Field must not be empty. Provide a name for the rule to easily identify it. | |||
|- | |||
|2 | |||
|Protocol | |||
|Example: <code>TCP+UDP</code> | |||
|Select the protocol for the rule. | |||
Options typically include TCP+UDP, TCP, UDP, ICMP, Custom. | |||
|- | |||
|3 | |||
|Source zone | |||
|Example: <code>SW_LAN</code> | |||
|Select the source zone where the traffic is originating from. Options typically include EWAN2,SW_LAN,CWAN1,CWAN1_0,CWAN1_1,VPN | |||
|- | |||
|4 | |||
|Source MAC address [optional] | |||
|Example: <code>any</code> | |||
|'''any''': Leave as <code>any</code> if you don't want to specify a MAC address. | |||
|- | |||
|5 | |||
|Source IP address[optional] | |||
|Example: Leave blank if not needed. | |||
|Optionally specify an IP address or range. | |||
|- | |||
|6 | |||
|Source port | |||
|Example: <code>80, 443</code> (if matching traffic for web server ports) | |||
|Specify the source port or port range. | |||
|- | |||
|7 | |||
|Destination zone | |||
|Example: <code>SW_LAN</code> | |||
|Select the destination zone where the traffic is heading to. | |||
|- | |||
|8 | |||
|Destination IP address | |||
|Leave blank if not needed. | |||
|Optionally specify the destination IP address or range. | |||
|- | |||
|9 | |||
|Destination port | |||
|Example: <code>80</code> (if redirecting to a web server port) | |||
|Specify the destination port or port range. | |||
|} | |||
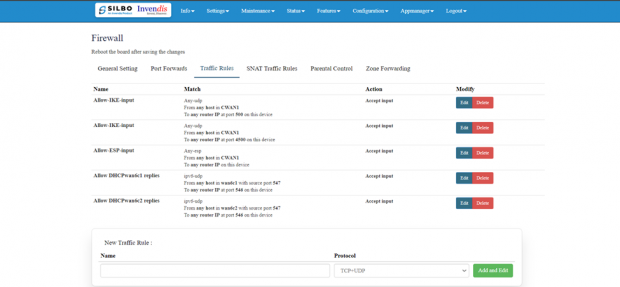
'''Traffic Rule:''' | |||
"Traffic rules" refer to the policies and regulations that govern the flow of data packets within a network. | |||
To allow new traffic, click on “Add and Edit” in “New Traffic Rule”. | |||
[[File:Firewall Traffic Rule Dashboard.png|frameless|620x620px]] | |||
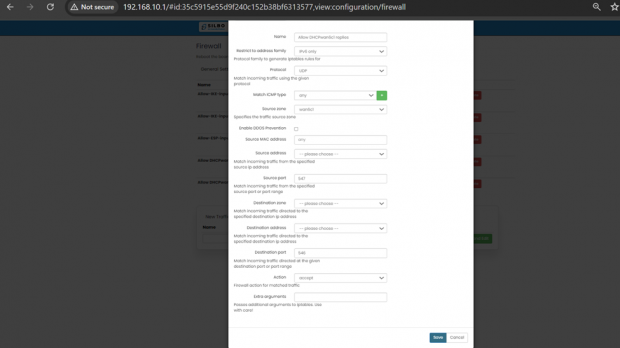
EDIT: | |||
[[File:Firewall Edit Options .png|frameless|620x620px]] | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Name | |||
|Example: Allow_HTTP_and_HTTPS | |||
|Field must not be empty: Provide a descriptive name for the traffic rule. | |||
|- | |||
|2 | |||
|Restrict to Address Family | |||
|1. Options: IPv4, IPv6 | |||
Example: IPv4 if dealing with typical internet traffic. | |||
|Select the address family to generate iptables rules for. | |||
|- | |||
|3 | |||
|Protocol | |||
|Example: TCP+UDP | |||
|TCP+UDP: Match incoming traffic using the given protocol. | |||
|- | |||
|4 | |||
|Match ICMP Type | |||
|Example: any | |||
|Match all ICMP types if set to any. Specific types can be chosen if needed. | |||
|- | |||
|5 | |||
|Source Zone | |||
|Example: LAN | |||
|Specifies the traffic source zone. | |||
|- | |||
|6 | |||
|Enable DDoS Prevention | |||
|Example: ‘Checked’ if you want to enable DDoS prevention measures | |||
|Enable or disable Distributed Denial of Service (DDoS) prevention. | |||
|- | |||
|7 | |||
|Source MAC Address | |||
|Example: any | |||
|any: Match traffic from any MAC address or specify a particular MAC address. | |||
|- | |||
|8 | |||
|Source Address | |||
|Example: 192.168.1.0/24 | |||
|Match incoming traffic from the specified source IP address or range. | |||
|- | |||
|9 | |||
|Source Port | |||
|Example: any if all source ports should be matched | |||
|any: Match incoming traffic from the specified source port or port range. | |||
|- | |||
|10 | |||
|Destination Zone | |||
|Example: WAN | |||
|Specifies the traffic destination zone. | |||
|- | |||
|11 | |||
|Action | |||
|Example: ACCEPT | |||
|Options: ACCEPT, DROP, REJECT. Specify the action to take for matched traffic. | |||
|- | |||
|12 | |||
|Limit | |||
|Example: 10/minute to limit matches to 10 times per minute. | |||
|Maximum average matching rate; specified as a number, with an optional /second, /minute, /hour, or /day suffix. | |||
|- | |||
|13 | |||
|Extra arguments | |||
|Example: --log-prefix "Blocked: " to add a log prefix to log messages for this rule. | |||
|Passes additional arguments to iptables. Use with care as it can significantly alter rule behaviour. | |||
|} | |||
Click on save once configured. | |||
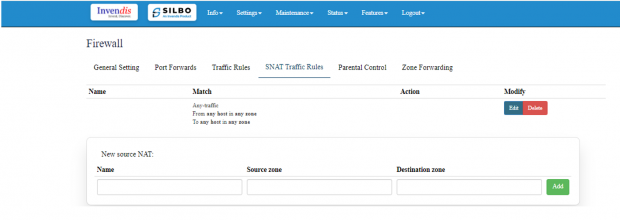
'''SNAT Traffic Rule:''' | |||
For configuring SNAT (Source Network Address Translation) traffic rules, you can control how outbound traffic from your local network is translated to a different IP address as it exits the network. | |||
To add new source NAT, | |||
Click on “ADD” in “New Source NAT:” | |||
[[File:SNAT Traffic Rule.png|frameless|620x620px]] | |||
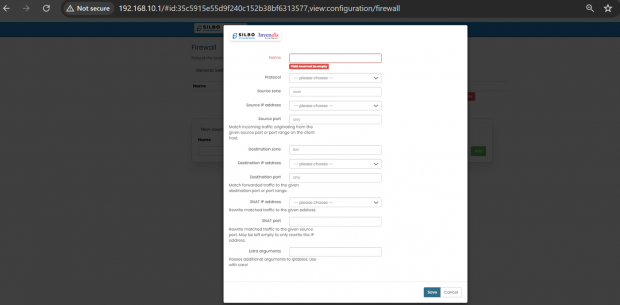
'''EDIT:''' | |||
[[File:SNAT Edit Options RC44.png|frameless|620x620px]] | |||
Specification details are below: | |||
{| class="wikitable" | |||
|SN | |||
|Field name | |||
|Sample value | |||
|Description | |||
|- | |||
|1 | |||
|Name | |||
|Example: SNAT_WAN_to_LAN | |||
|'''Field must not be empty''': Provide a unique and descriptive name for the SNAT rule. | |||
|- | |||
|2 | |||
|Protocol | |||
|Example: TCP+UDP | |||
|'''TCP+UDP''': Select the protocols that the SNAT rule will apply to. | |||
|- | |||
|3 | |||
|Source Zone | |||
|Example: wan | |||
|'''wan''': Specifies the source zone from which the traffic originates. | |||
|- | |||
|4 | |||
|Source IP Address | |||
|Example: any or a specific range like 192.168.1.0/24 | |||
|'''-- please choose --''': Specify the source IP address or range. Leave empty if the rule applies to any source IP. | |||
|- | |||
| | |||
| | |||
| | |||
| | |||
|- | |||
|5 | |||
|Source Port | |||
|Example: any | |||
|'''any''': Specify the source port or port range from which the traffic originates. | |||
|- | |||
|6 | |||
|Destination Zone | |||
|Example: lan | |||
|'''lan''': Specifies the destination zone to which the traffic is directed. | |||
|- | |||
|7 | |||
|Destination IP Address | |||
|Example: any or a specific IP like 192.168.1.100 | |||
|'''-- please choose --''': Specify the destination IP address or range. Leave empty if the rule applies to any destination IP. | |||
|- | |||
|8 | |||
|Destination port | |||
|Example: any | |||
|'''any''': Specify the destination port or port range to which the traffic is directed. | |||
|- | |||
|9 | |||
|SNAT IP Address | |||
|Example: 203.0.113.5 (an external IP address) | |||
|'''-- please choose --''': Specify the IP address to which the source IP should be translated. | |||
|- | |||
|10 | |||
|SNAT Port | |||
|Example: Leave empty if not needed, or specify a port like ‘12345’ | |||
|Optionally, rewrite matched traffic to a specific source port. Leave empty to only rewrite the IP address. | |||
|- | |||
|11 | |||
|Extra Arguments | |||
|Example: --log-prefix "SNAT_traffic: " (to add a log prefix to log messages for this rule) | |||
|Pass additional arguments to iptables. Use with care as it can significantly alter rule behaviour. | |||
|} | |||
Click on save once configured. | |||
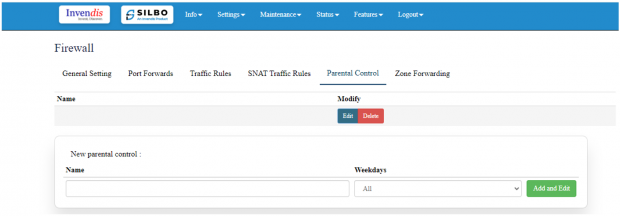
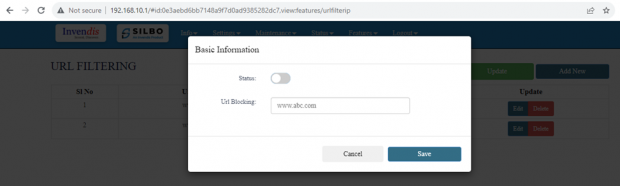
'''Parental Control:''' | |||
For configuring parental control rules, you want to set restrictions based on time, source, and | |||
destination zones, as well as specific devices. | |||
To add parental control in firewall, | |||
Click on “Add and Edit” in “New parental control:” field. | |||
[[File:Parental Control.png|frameless|620x620px]] | |||
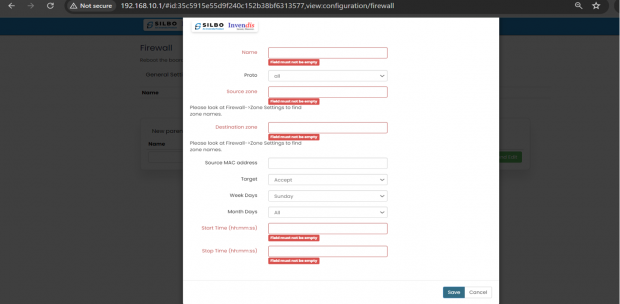
'''EDIT:''' | |||
[[File:Parental Control Edit Options RC44.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Name | |||
|Example: Parental_Control_Sunday | |||
|'''Field must not be empty''': Provide a unique and descriptive name for the parental control rule. | |||
|- | |||
|2 | |||
|Proto | |||
|all | |||
|'''all''': This specifies that the rule will apply to all protocols. | |||
|- | |||
|3 | |||
|Source Zone | |||
|Example: lan | |||
|'''Field must not be empty''': Please look at Firewall->Zone Settings to find zone names. | |||
|- | |||
|4 | |||
|Destination Zone | |||
|Example: wan | |||
|'''Field must not be empty''': Please look at Firewall->Zone Settings to find zone names. | |||
|- | |||
|5 | |||
|Source MAC Address | |||
|Example: 00:1A:2B:3C:4D:5E | |||
|'''Field''': Enter the MAC address of the device you want to apply the parental control rule to. This is useful for restricting specific devices. | |||
|- | |||
|6 | |||
|Target | |||
|Example: Reject | |||
|'''Accept''': This specifies the action to take. For parental controls, you might want to use ‘Reject’ or ‘Drop’ to block traffic. | |||
|- | |||
|7 | |||
|Weekdays | |||
|Example: Sunday | |||
|'''Sunday''': Specify the days of the week when the rule should be active. | |||
|- | |||
|8 | |||
|Month Days | |||
|Example: All | |||
|'''All:''' Specify the days of the month when the rule should be active. | |||
|- | |||
|9 | |||
|Start Time (hh:mm:ss) | |||
|Example: 18:00:00 (6:00 PM) | |||
|'''Field must not be empty:''' Specify the start time when the rule should begin to apply. | |||
|- | |||
|10 | |||
|Stop Time (hh:mm:ss) | |||
|Example: 22:00:00 (10:00 PM) | |||
|'''Field must not be empty:''' Specify the stop time when the rule should end. | |||
|} | |||
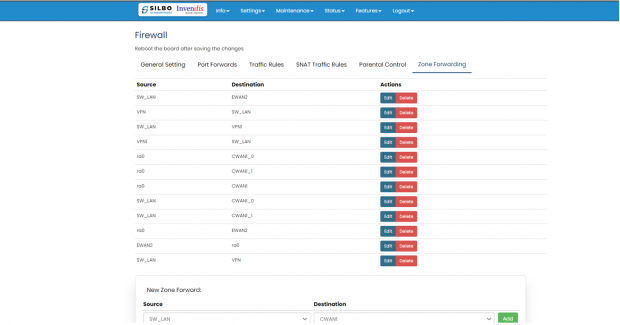
'''Zone Forwarding:''' | |||
Zone forwarding in network configuration allows traffic to be directed from one zone to another. | |||
To ADD new zone, | |||
Click on “Add” in “New Zone Forward:” field. | |||
[[File:Zone Forwarding RC44.png|frameless|620x620px]] | |||
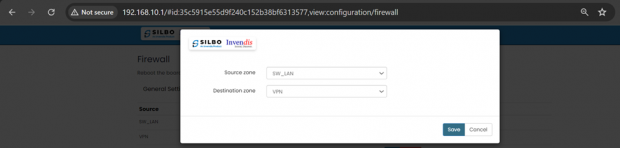
'''EDIT:''' | |||
[[File:Parental Control Zone Configuration.png|frameless|620x620px]] | |||
Specification details are below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Source Zone | |||
|Example options: lan, wan, etc. | |||
|'''--please choose--''': Select the source zone from which the traffic originates. | |||
|- | |||
|2 | |||
|Destination Zone | |||
|Example options: lan, wan, etc. | |||
|'''--please choose--''': Select the destination zone to which the traffic is directed. | |||
|} | |||
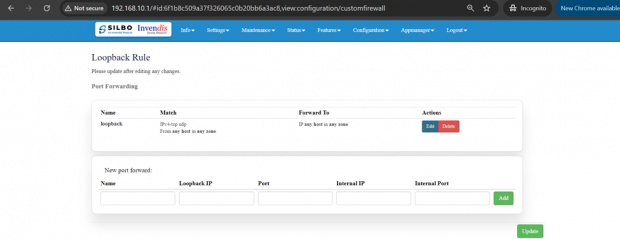
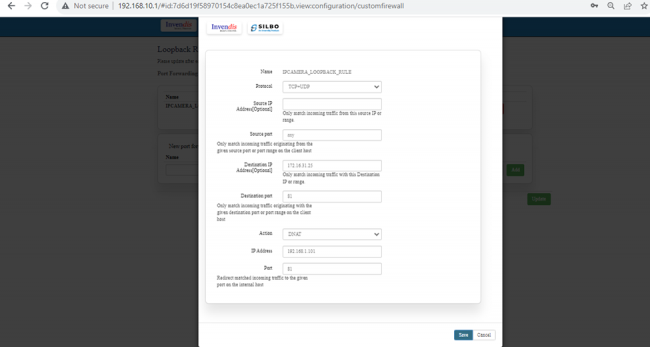
=== 2.6 Loopback Rule === | |||
In this page the user can configure the port where he wants to forward the traffic to. Here the user can add/edit/delete different ports as per the requirement. | |||
[[File:Parental Control Zone Loopback Rule.png|frameless|620x620px]] | |||
The user should click on ‘add’ and then ‘edit’ to do the required changes in the port and enter the valid information in each section to configure the port for forwarding. | |||
'''EDIT:''' | |||
[[File:Parental Control Zone Loopback Rule 1.png|frameless|650x650px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Name | |||
|Example: loopback | |||
|Provide a descriptive name for the rule. | |||
|- | |||
|2 | |||
|Protocol | |||
|Example: TCP+UDP | |||
|'''TCP+UDP''': Select the protocols that the rule will apply to. | |||
|- | |||
|3 | |||
|Source IP Address [Optional] | |||
|Example: any or a specific IP range like 192.168.1.0/24 | |||
|Optionally specify the source IP address or range. Leave empty if the rule should apply to any source IP. | |||
|- | |||
|4 | |||
|Source Port [Optional] | |||
|Example: any | |||
|'''any''': Specify the source port or port range from which the traffic originates. any allows traffic from all ports. | |||
|- | |||
|5 | |||
|Loopback IP Address | |||
|Example: 127.0.0.1 | |||
|Specify the loopback IP address. Typically, this is 127.0.0.1. | |||
|- | |||
|6 | |||
|Port | |||
|Example: any | |||
|'''any''': Specify the destination port or port range to which the traffic is directed. any allows traffic to all ports. | |||
|- | |||
|7 | |||
|Action | |||
|Example: DNAT | |||
|This specifies the action to take either DNAT or SNAT. | |||
|- | |||
|8 | |||
|Internal IP Address | |||
|Example: 192.168.1.100 | |||
|'''Field must not be empty''': Specify the internal IP address to which the traffic should be redirected. | |||
|- | |||
|9 | |||
|Internal Port | |||
|Example: any | |||
|Redirect matched incoming traffic to the given port on the internal host. | |||
|} | |||
Once the user is done with the required configurations, should click save button and then click on the update to save the changes. | |||
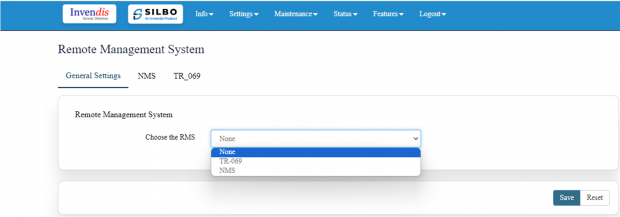
=== 2.7 Remote Monitoring === | |||
In this page the user can select which equipment needs to be monitored remotely. | |||
Once the user selects the type of RMS click on save. | |||
[[File:Remote Monitoring.png|frameless|620x620px]] | |||
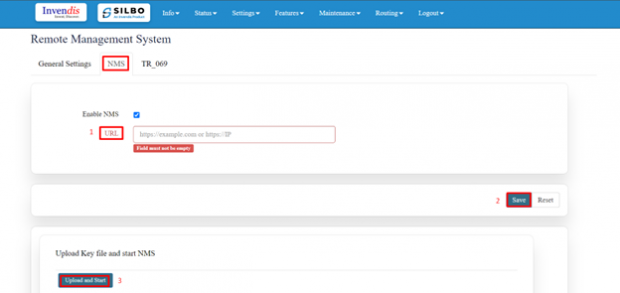
'''NMS:''' | |||
IN this page the user should type the server IP or domain name in the URL then click on save. | |||
Click on upload and start (Once key is uploaded and this option is clicked, NMS automatically starts, and this router device gets registered with the NMS server provided). | |||
[[File:Remote Management System NMS Configuration.png|frameless|620x620px]] | |||
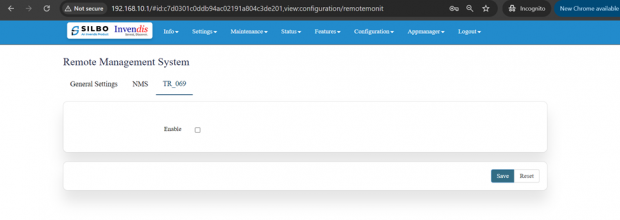
'''TR_069:''' | |||
To enable the TR_069 the user needs to click on the enable check box. | |||
[[File:TR 069.png|frameless|620x620px]] | |||
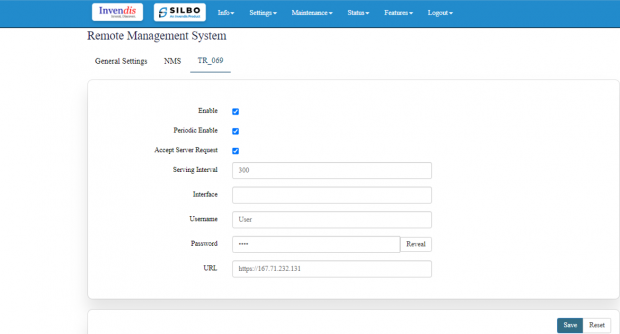
Once the user clicks on the check box of enable it will display all the required filed to configured. | |||
[[File:Remote Monitoring Tr-069.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Serving Interval | |||
|300 | |||
|A value of 300 seconds means the device will check in with the ACS (auto-configuration servers) every 5 minutes. | |||
|- | |||
|2 | |||
|Interface | |||
|This can be something like eth0 or wan. | |||
|This specifies the network interface used for TR-069 communication. | |||
|- | |||
|3 | |||
|Username | |||
|Example: User | |||
|The username used to authenticate with the ACS. | |||
|- | |||
|4 | |||
|Password | |||
|•••• | |||
|The password used to authenticate with the ACS. | |||
|- | |||
|5 | |||
|URL | |||
|<nowiki>http://example.com</nowiki> | |||
|The URL of the ACS. This is where the CPE (customer-premises equipment) will send its requests and where it will receive configurations and updates from. | |||
|} | |||
The user should fill all the required fields and click on the save button. | |||
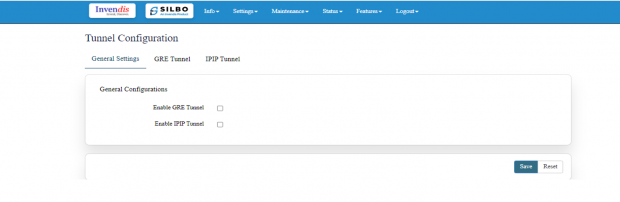
=== 2.8 Tunnel === | |||
Tunnels are a method of transporting data across a network using protocols which are not supported by that network. | |||
It is further categorised into 3 sections, | |||
1.) General Settings | |||
2.) GRE Tunnel | |||
3.) IPIP Tunnel | |||
[[File:Tunnel Settings.png|frameless|620x620px]] | |||
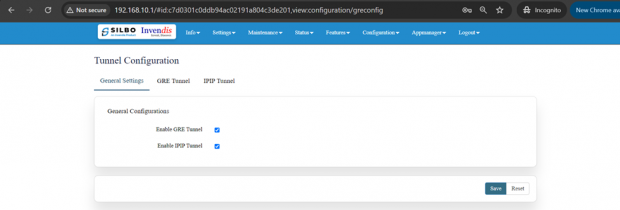
'''General Settings:''' | |||
In this page the user needs to select under which type of tunnel it needs to send the data. | |||
[[File:Tunnel General Settings 1.png|frameless|620x620px]] | |||
Once the user selects the type of tunnel then click on the save button. | |||
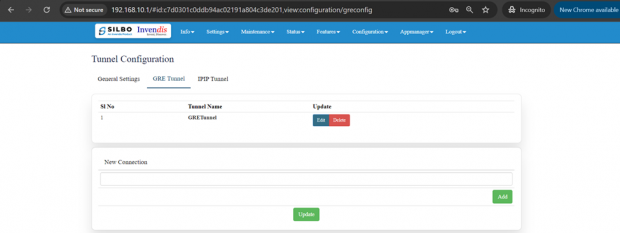
'''GRE Tunnel:''' | |||
A GRE (Generic Routing Encapsulation) tunnel configuration involves setting up a virtual point-to-point connection between two endpoints over an IP network. | |||
Here the user can add/edit/delete the details of the tunnel. | |||
[[File:GRE Dashboard.png|frameless|620x620px]] | |||
Once the required update is done then click on update to save the changes. | |||
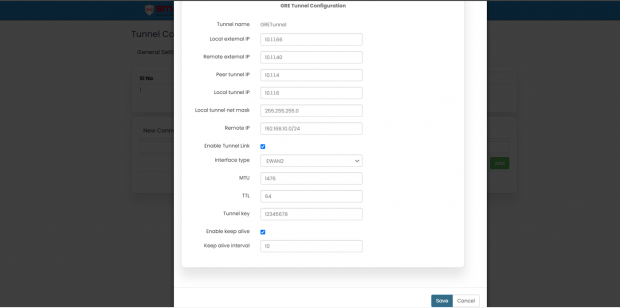
'''EDIT:''' | |||
[[File:GRE Tunnel.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Tunnel name | |||
|Example: GRETunnel | |||
|'''GRETunnel''': The name of the GRE tunnel. | |||
|- | |||
|2 | |||
|Local external IP | |||
|Example: 10.1.1.66 | |||
|The IP address of the local endpoint that will initiate the GRE tunnel. | |||
|- | |||
|3 | |||
|Remote external IP | |||
|Example: 10.1.1.40 | |||
|The IP address of the remote endpoint that will terminate the GRE tunnel. | |||
|- | |||
|4 | |||
|Peer tunnel IP | |||
|Example: 10.1.1.4 | |||
|The IP address of the peer's tunnel interface. | |||
|- | |||
|5 | |||
|Local tunnel IP | |||
|Example: 10.1.1.6 | |||
|The IP address of the local tunnel interface. | |||
|- | |||
|6 | |||
|Local tunnel net mask | |||
|Example: 255.255.255.0 | |||
|The subnet mask of the local tunnel interface. | |||
|- | |||
|7 | |||
|Remote IP | |||
|Example: 192.168.10.0/24 | |||
|The remote network that is reachable through the GRE tunnel. | |||
|- | |||
|8 | |||
|Enable Tunnel Link | |||
|Check to enable | |||
|Enable or disable the GRE tunnel link. | |||
|- | |||
|9 | |||
|Interface type | |||
|Example: EWAN2 | |||
|'''EWAN2''': The type of network interface used for the GRE tunnel. | |||
|- | |||
|10 | |||
|MTU | |||
|Example: 1476 | |||
|'''1476''': Maximum Transmission Unit size for the GRE tunnel. | |||
|- | |||
|11 | |||
|TTL | |||
|Example: 64 | |||
|'''64''': Time To Live value for the packets within the GRE tunnel. | |||
|- | |||
|12 | |||
|Tunnel key | |||
|Example: 12345678 | |||
|'''12345678''': A unique key used to identify the GRE tunnel. | |||
|- | |||
|13 | |||
|Enable keep alive | |||
|Check to enable | |||
|Enable or disable the keep-alive feature to monitor the tunnel's status. | |||
|- | |||
|14 | |||
|Keep alive interval | |||
|Example: 10 | |||
|'''10''': Interval in seconds for the keep-alive packets. | |||
|} | |||
Once the required update is done then click on update to save the changes. | |||
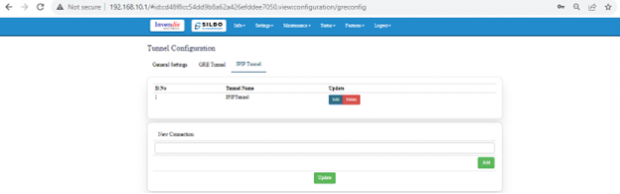
'''IPIP Tunnel:''' | |||
An IPIP (IP-in-IP) tunnel is a simple tunnelling protocol used to encapsulate IP packets within IP packets. This is like GRE but without additional features such as keying and type fields. | |||
Here the user can add/edit/delete the details of the tunnel. | |||
[[File:Ipip config.png|frameless|620x620px]] | |||
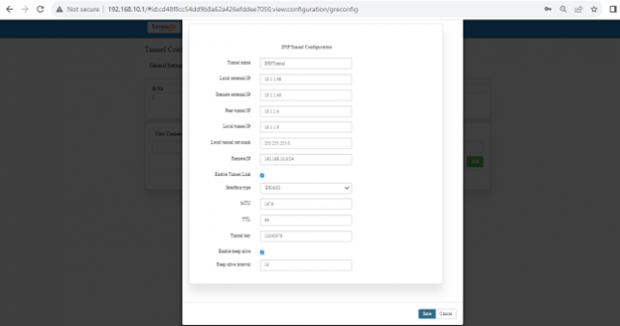
'''EDIT:''' | |||
[[File:IPIP Tunnel.png|frameless|620x620px]] | |||
Once the required update is done then click on update to save the changes. | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Tunnel name | |||
|Example: IPIPTunnel | |||
|'''IPIPTunnel:''' The name of the IPIP tunnel. | |||
|- | |||
|2 | |||
|Local external IP | |||
|Example: 10.1.1.66 | |||
|The IP address of the local endpoint that will initiate the IPIP tunnel. | |||
|- | |||
|3 | |||
|Remote external IP | |||
|Example: 10.1.1.40 | |||
|The IP address of the remote endpoint that will terminate the IPIP tunnel. | |||
|- | |||
|4 | |||
|Peer tunnel IP | |||
|Example: 10.1.1.4 | |||
|The IP address of the peer's tunnel interface. | |||
|- | |||
|5 | |||
|Local tunnel IP | |||
|Example: 10.1.1.6 | |||
|The IP address of the local tunnel interface. | |||
|- | |||
|6 | |||
|Local tunnel net mask | |||
|Example: 255.255.255.0 | |||
|The subnet mask of the local tunnel interface. | |||
|- | |||
|7 | |||
|Remote IP | |||
|Example: 192.168.10.0/24 | |||
|The remote network that is reachable through the IPIP tunnel. | |||
|- | |||
|8 | |||
|Enable Tunnel Link | |||
|Check to enable | |||
|Enable or disable the IPIP tunnel link. | |||
|- | |||
|9 | |||
|Interface type | |||
|Example: EWAN2 | |||
|'''EWAN2''': The type of network interface used for the IPIP tunnel. | |||
|- | |||
|10 | |||
|MTU | |||
|Example: 1476 | |||
|'''1476''': Maximum Transmission Unit size for the IPIP tunnel. | |||
|- | |||
|11 | |||
|TTL | |||
|Example: 64 | |||
|'''64''': Time To Live value for the packets within the IPIP tunnel. | |||
|- | |||
|12 | |||
|Tunnel key | |||
|Example: 12345678 | |||
|Although typically not used in IPIP, this field might be included for compatibility with certain configurations. | |||
|- | |||
|13 | |||
|Enable keep alive | |||
|Check to enable | |||
|Enable or disable the keep-alive feature to monitor the tunnel's status. | |||
|- | |||
|14 | |||
|Keep alive interval | |||
|Example: 10 | |||
|'''10''': Interval in seconds for the keep-alive packets. | |||
|} | |||
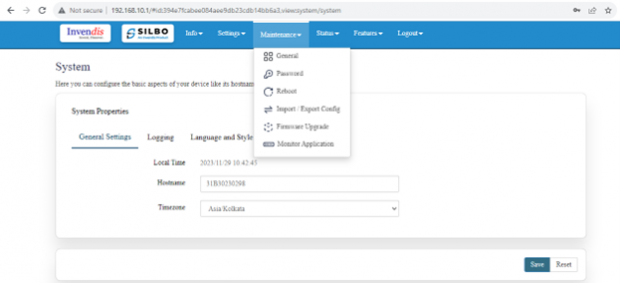
= 3.Maintenance = | |||
In this module the user can configure/upgrade/modify the settings related to system, password, | |||
firmware and monitoring. | |||
It includes 6 submodules. | |||
* General | |||
* Password | |||
* Reboot | |||
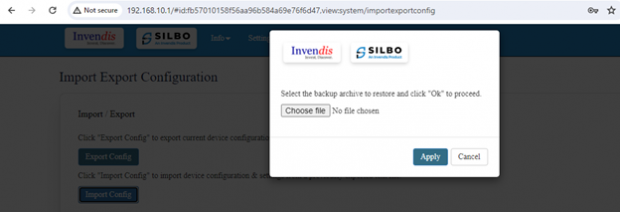
* Import and Export config | |||
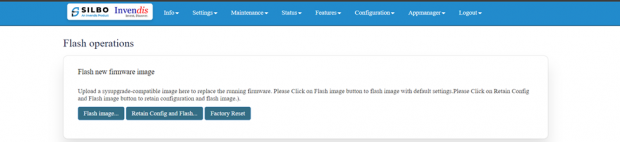
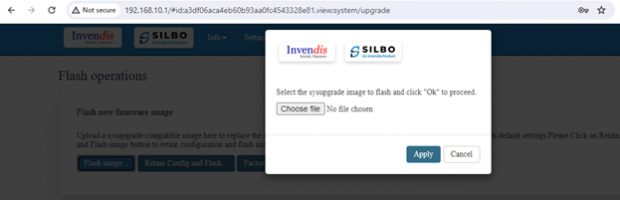
* Firmware upgrade | |||
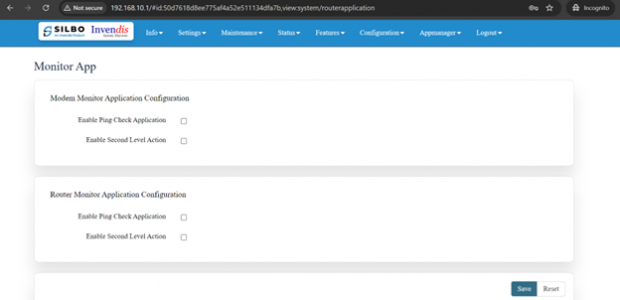
* Monitor Application | |||
[[File:Maintenance System.png|frameless|620x620px]] | |||
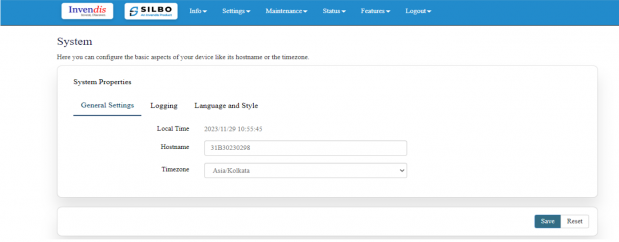
=== 3.1 General === | |||
Here you can configure the basic aspects of router like its hostname or the timezone. | |||
It is further sub-divided into, | |||
1.) General Settings | |||
2.) Logging | |||
3.) Language and Style | |||
'''General Settings:''' | |||
[[File:Maintenance General.png|frameless|619x619px]] | |||
'''EDIT:''' | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Local Time | |||
|2024/07/30 13:25:47 | |||
|The current local date and time set on the device. | |||
|- | |||
|2 | |||
|Hostname | |||
|22B25240007 | |||
|The hostname of the device, which is used to identify it on the network. | |||
|- | |||
|3 | |||
|Timezone | |||
|Asia/Kolkata | |||
|The timezone setting of the device, which determines the local time. | |||
|} | |||
Once the user configures the required details then click on the save button to save all the details. | |||
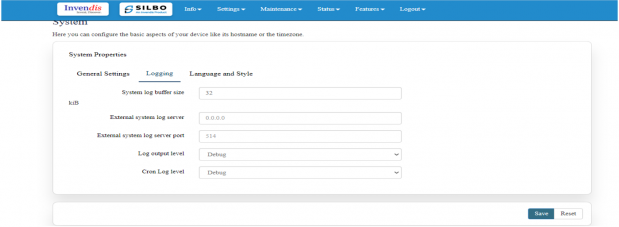
'''Logging:''' | |||
Here the user can configure the basic aspects of your device related to system. | |||
The system log configuration provided specifies how the device handles and stores log information, including buffer size, external log server details, and log verbosity levels. | |||
[[File:Maintenance logging.png|frameless|619x619px]] | |||
'''EDIT:''' | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|System log buffer size | |||
|Example: 32 kiB | |||
|The size of the memory buffer allocated (0-32) for storing system logs before they are either written to a file or sent to an external server. | |||
|- | |||
|2 | |||
|External system log server | |||
|Example: 0.0.0.0 | |||
|The IP address of an external server where logs can be sent. | |||
|- | |||
|3 | |||
|External system log server port | |||
|Example: 514 | |||
|The port used to send logs to the external log server. Port 514 is the default port for syslog. | |||
|- | |||
|4 | |||
|Log output level | |||
|Example: Debug | |||
|Sets the detail level of the system logs. | |||
|- | |||
|5 | |||
|Cron Log level | |||
|Example: Debug | |||
|The detail level of the logs for cron jobs. | |||
|} | |||
Once the user configures the required details then click on the save button to save all the details. | |||
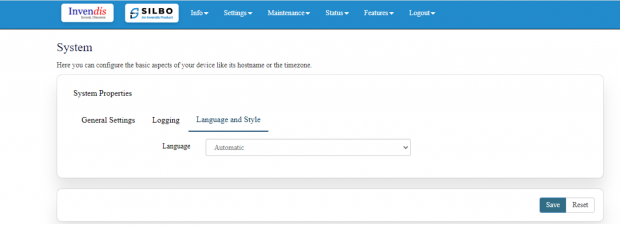
'''Language and Style:''' | |||
Here the user can configure the basic aspects of your device related to language. | |||
Once the user configures the required details then click on the save button to save all the details. | |||
[[File:Maintenance Language and Style.png|frameless|620x620px]] | |||
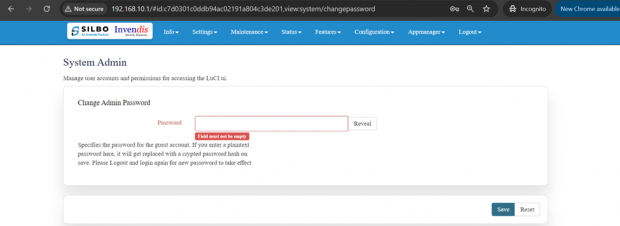
=== 3.2 Password === | |||
In this module the user can set the password for the admin credentials. | |||
Specifies the password for the guest account. If the user enters a plaintext password here, it will get replaced with a crypted password on save. The new password will be effective once the user logs out and log in again. | |||
[[File:Admin Password Setup.png|frameless|620x620px]] | |||
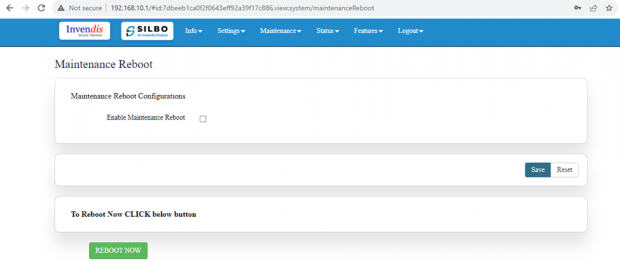
=== 3.3 Reboot === | |||
In this module the user can reboot the device remotely. | |||
First option is to directly reboot the device without enabling the maintenance reboot tab. | |||
Click on “Reboot Now” at the bottom of the screen to start the reboot process. | |||
[[File:Reboot Dashboard enable.png|frameless|620x620px]] | |||
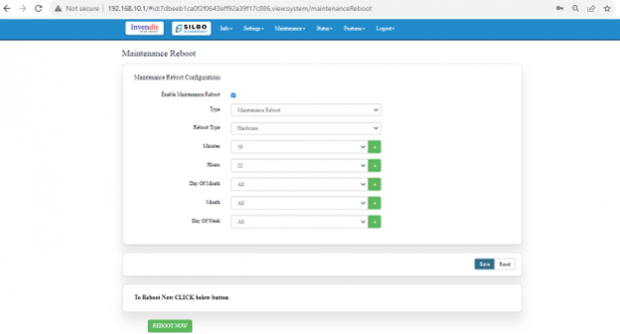
To start maintenance reboot process first the user needs to fill all the required fields. | |||
Need to select the type of reboot for the device whether it needs to be Hardware or Software reboot. | |||
[[File:Maintenance Reboot.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Enable Maintenance Reboot | |||
|Enable/Disable | |||
|Indicates whether the maintenance reboot feature is enabled or not. | |||
|- | |||
|2 | |||
|Type | |||
|Maintenance Reboot | |||
|Specifies the type of reboot being scheduled. | |||
|- | |||
|3 | |||
|Reboot Type | |||
|Software/Hardware | |||
|'''Hardware''': A hardware reboot involves restarting the entire device as if it were powered off and on again. | |||
'''Software''': A software reboot involves restarting the operating system without powering off the hardware. | |||
|- | |||
|4 | |||
|Minutes | |||
|Example: 59 | |||
|The minute at which the reboot should occur (0-59). | |||
|- | |||
|5 | |||
|Hours | |||
|Example: 22 (10 PM) | |||
|The hour at which the reboot should occur (0-23, in 24-hour format). | |||
|- | |||
|6 | |||
|Day Of Month | |||
|Example: All | |||
|Specifies which days of the month the reboot should occur (1-31). "All" means it will occur every day. | |||
|- | |||
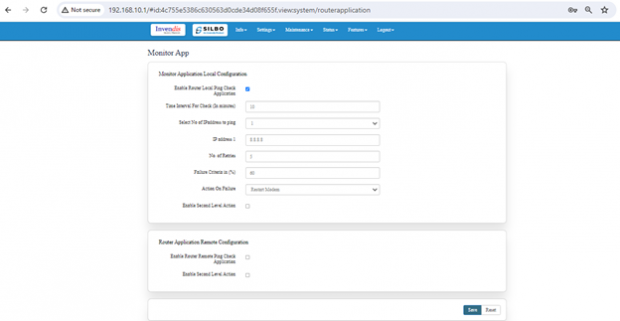
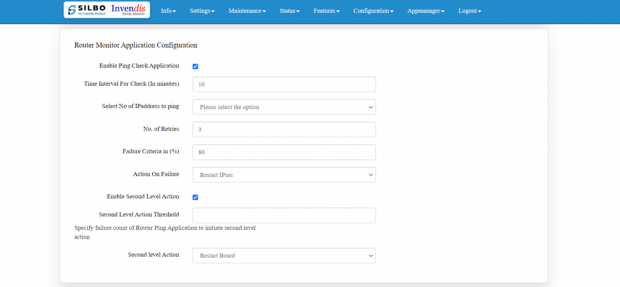
|7 | |||
|Month | |||
|Example: All | |||
|Specifies which months the reboot should occur (1-12). "All" means it will occur every month. | |||
|- | |||
|8 | |||
|Day Of Week | |||
|Example: All | |||
|Specifies which days of the week the reboot should occur (0-6, where 0 is Sunday). "All" means it will occur every day of the week. | |||
|} | |||
Once the user fills all the required given parameters click on the save. | |||
=== 3.4 Import and Export === | |||
In this section, User can Import & Export Configuration files of the Device. | |||
[[File:Import and Export Options.png|frameless|601x601px]] | |||
Click “Export Config” to export device configuration & settings to a text file, | |||
Click “Import Config” to import device configuration & settings from a previously exported text file. | |||
[[File:Import window.png|frameless|620x620px]] | |||
The user needs to select on the “choose file”, upload the required file and click on apply. | |||
=== 3.5 Firmware Upgrade === | |||
The user can upgrade with the latest software for the existing firmware. | |||
[[File:Firmware Upgrade .png|frameless|620x620px]] | |||
Click on the '''flash image''' and chose the path where the sys-upgrade file is kept and then click on flash image, it will upgrade to the latest software once the reboot is done. | |||
This option will completely reset the device to default settings. | |||
[[File:Flash Image.png|frameless|620x620px]] | |||
Click on the '''Retain Config and flash''' and chose the path where the sys-upgrade file is kept and then click on Retain Config and flash, it will upgrade to the latest software once the reboot is done. | |||
This refers to updating the firmware (flashing) of a device while preserving the current configuration settings. | |||
[[File:Flash Image.png|frameless|620x620px]] | |||
Click on the '''Factory Reset''' for the complete retest of the device. | |||
=== 3.6 Monitor Application === | |||
In this section, the monitor application is divided into major 2 configurations which is further sub-divided into 4 editable options, | |||
1.) Modem Monitor Application Configuration: | |||
2.) Router Monitor Application Configuration: | |||
[[File:Monitor Application Dashboard.png|frameless|620x620px]] | |||
'''Modem Monitor Application Configuration:''' | |||
[[File:Monitor Application.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Enable Ping Check Application | |||
|Enable/Disable | |||
|Turns on the functionality to perform ping checks on specified IP addresses. | |||
|- | |||
|2 | |||
|Time Interval for Check (In minutes) | |||
|'''Example:''' 10 minutes | |||
|Frequency at which the ping checks are performed. | |||
|- | |||
|3 | |||
|Select No of IP addresses to ping | |||
|'''Example:''' 1 | |||
|Number of IP addresses that will be pinged. | |||
|- | |||
|4 | |||
|IP Address 1 | |||
|'''Example:''' 8.8.8.8 | |||
|The IP address to ping. | |||
|- | |||
|5 | |||
|No. of Retries | |||
|'''Example:''' 5 | |||
|Number of times to retry pinging an IP address if the initial ping fails. | |||
|- | |||
|6 | |||
|Failure Criteria in (%) | |||
|'''Example:''' 80% (If 4 out of 5 pings fail, it’s considered a failure) | |||
|Percentage of failed pings required to consider the ping check a failure. | |||
|- | |||
|7 | |||
|Action On Failure | |||
|'''Example:''' Restart Modem | |||
|Action to be taken if the ping check fails according to the criteria. | |||
|- | |||
|8 | |||
|Enable Second Level Action | |||
|Enable/Disable | |||
|Option to enable a secondary action if the primary action fails multiple times. | |||
|- | |||
|9 | |||
|Second Level Action Threshold | |||
|'''Example:''' 2 | |||
|Number of failures required to trigger the secondary action. | |||
|- | |||
|10 | |||
|Second Level Action | |||
|'''Example:''' Restart Board (Reboots the entire hardware board) | |||
|The action to be taken if the second level action threshold is met. | |||
|} | |||
Save the details once made necessary changes. | |||
'''Router Monitor Application Configuration:''' | |||
[[File:Router Monitor Application Configuration.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Enable Ping Check Application | |||
|Enable/Disable | |||
|Activates the ping check functionality to monitor router performance. | |||
|- | |||
|2 | |||
|Time Interval for Check (In minutes) | |||
|'''Example:''' 10 minutes | |||
|How frequently the ping checks are performed. | |||
|- | |||
|3 | |||
|Select No of IP Addresses to Ping | |||
|'''Example:''' 1 (Please select the appropriate number based on your requirements) | |||
|Choose the number of IP addresses to ping. This typically involves selecting from a list or entering multiple addresses. | |||
|- | |||
|4 | |||
|No. of Retries | |||
|'''Example:''' 3 | |||
|Number of retries if a ping fails. | |||
|- | |||
|5 | |||
|Failure Criteria in (%) | |||
|'''Example:''' 80% (If 80% of the pings fail, it’s deemed a failure) | |||
|Percentage of failed pings required to consider the ping check as failed. | |||
|- | |||
|6 | |||
|Action On Failure | |||
|'''Example:''' Restart IPsec | |||
|The action taken if the ping check fails according to the criteria. | |||
|- | |||
|7 | |||
|Enable Second Level Action | |||
|Enable/Disable | |||
|Option to enable an additional action if the primary action fails. | |||
|- | |||
|8 | |||
|Second Level Action Threshold | |||
|'''Example:''' Specify the number of failures, such as 2 | |||
|Number of times the primary action must fail before the secondary action is triggered. | |||
|- | |||
|9 | |||
|Second Level Action | |||
|'''Example:''' Restart Board | |||
|The action to be taken if the second level action threshold is met. | |||
|} | |||
Save the details once made necessary changes. | |||
= 4.Status = | |||
In this module the user can view the status of the router device with respect to the network, Wan, modem etc. | |||
It has 4 submodules. | |||
* Interfaces | |||
* Internet | |||
* Modem | |||
* Routes | |||
[[File:Status Dashboard.png|frameless|620x620px]] | |||
=== 4.1 Interfaces === | |||
Each network device (interface) is associated with specific traffic statistics, uptime, and status. Active interfaces are operational, while inactive interfaces are not currently transmitting data. | |||
[[File:Status Interfaces.png|frameless|620x620px]] | |||
Looking on the network status the user can check if the cellular, wifi, ewan, vpn etc is up. | |||
=== 4.2 Internet === | |||
In this submodule the user can view the status of the internet connections. | |||
[[File:Internet Status.png|frameless|620x620px]] | |||
To see the latest status of the internet connection the user needs to click on the refresh button. | |||
=== 4.3 Modem === | |||
This modem status page provides comprehensive information about the cellular connection's network operator, technology, mode, and various signal quality metrics. | |||
[[File:Modem Status.png|frameless|602x602px]] | |||
=== 4.4 Routes === | |||
This configuration shows how the router directs traffic between different networks and interfaces, ensuring proper communication within the local network and to external networks via the default gateway. | |||
'''ARP Table:''' Maps IP addresses to MAC addresses for devices on the network, helping in identifying which device is on which interface. | |||
'''IPv4 Routes:''' This shows which network is directly connected on which interface. | |||
Example: Network '''192.168.10.0/24''' is directly connected on interface '''eth0.1.''' | |||
'''IPv6 Routes:''' Similar routes as IPv4, but this time listed under IPv6 routing rules. | |||
Example: Local networks '''192.168.10.0/24''' and '''192.168.100.0/24''' are managed through '''eth0.1''' and '''ra0''', respectively. | |||
[[File:Route Status.png|frameless|620x620px]] | |||
= 5. Features = | |||
In this module the user can see all the features that the router device has. | |||
This module includes 7 features. | |||
* Mac Address Binding | |||
* URL Filtering | |||
* Web Server | |||
* Wi-Fi MacID Filtering | |||
* Routing | |||
* Others | |||
[[File:Features.png|frameless|618x618px]] | |||
=== 5.1 Mac Address Binding === | |||
MAC address binding is a configuration that binds a specific MAC address to a specific IP address. This ensures that a particular device on the network always receives the same IP address from the DHCP server, which can be useful for network management, security, and ensuring consistent network behaviour. | |||
Under this submodule the user can configure/update/edit the IP Address for MAC. | |||
You can edit the pre-existing configuration, or you can ‘Add’ in the ‘New MAC ADDRESS’ field. | |||
[[File:Mac Addressing Binding.png|frameless|620x620px]] | |||
'''EDIT:''' | |||
[[File:Mac Address Edit.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Device Name | |||
|Macbinding1 | |||
|A user-defined name for the binding configuration. | |||
|- | |||
|2 | |||
|MAC Address | |||
|48:9e:bd:da:45:91 | |||
|The unique identifier for the network interface of the device to which the IP address will be bound. | |||
|- | |||
|3 | |||
|IP Address | |||
|192.168.10.55 | |||
|The IP address that will be consistently assigned to the device with the specified MAC address. | |||
|} | |||
By applying this configuration, the DHCP server will always assign the IP address 192.168.10.55 to the device with the MAC address 48:9e:bd:da:45:91, ensuring consistency and stability in network addressing for that device. | |||
* Once the user modifies the MAC address /IP Address then click on the save button to save the changes done. | |||
* The user can click on the deleted button to delete an existing configured device. | |||
Post all the changes the user needs to click on the update to reflect all the changes in the application. | |||
=== 5.2 URL Filtering === | |||
In this submodule the user should provide the URL which needs to be blocked for the device. By implementing URL filtering with the specified URL, you can control and restrict access to certain websites, thereby improving network security and managing user access. | |||
[[File:URL Filtering.png|frameless|620x620px]] | |||
To add the new URL for blocking, click on the Add New button. | |||
Once the user clicks on the Add New button a new pop will appear in that page write the URL and click on the save. | |||
The user can select the status of that URL while defining the URL. | |||
[[File:Url Update.png|frameless|620x620px]] | |||
To edit / delete the existing URL the user needs to click on the edit /deleted button respectively. | |||
[[File:URL Filtering .png|frameless|620x620px]] | |||
Click on “save” after the changes are done as per the need. | |||
=== 5.3 Web Server === | |||
This configuration will allow your device to serve web traffic securely over HTTPS, keep its system time synchronized, and ensure that all HTTP traffic is redirected to HTTPS for better security. | |||
[[File:Web server.png|frameless|620x620px]] | |||
'''EDIT:''' | |||
[[File:Webserver Configuration Editing.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Enable HTTP | |||
|'''HTTP Port:''' 80 | |||
Enable or disable the HTTP server. | |||
|Port 80 is the default port for HTTP traffic. It is used to serve web pages over an unencrypted connection. | |||
|- | |||
|2 | |||
|Enable HTTPS | |||
|'''HTTPS Port:''' 443 | |||
Enable or disable the HTTPS server. | |||
|Port 443 is the default port for HTTPS traffic. It is used to serve web pages over an encrypted connection. | |||
|- | |||
|3 | |||
|Redirect HTTPS | |||
|Option to redirect HTTP traffic to HTTPS. | |||
|When enabled, all HTTP requests will be automatically redirected to the HTTPS port to ensure secure communication. | |||
|- | |||
|4 | |||
|Enable NTP Sync | |||
|Enable or disable NTP synchronization. | |||
|Synchronizes the device’s system clock with an external NTP server to maintain accurate time. | |||
|- | |||
|5 | |||
|NTP Server | |||
|0.openwrt.pool.ntp.org | |||
|The address of the NTP server used for time synchronization. The openwrt.pool.ntp.org server is a public NTP server pool. | |||
|- | |||
|6 | |||
|NTP Sync Interval (In Minutes) | |||
|15 | |||
|The interval at which the device will sync its clock with the NTP server, set to every 15 minutes in this case. | |||
|} | |||
Click on save once changes are made. | |||
=== 5.4 Wi-Fi MacID Filtering === | |||
Wireless MAC ID Filtering allows you to control which devices can connect to your wireless network based on their MAC (Media Access Control) addresses. This can help enhance security by allowing only specified devices to access the network. | |||
It is further divided into 2 categories, | |||
'''WIFI 2.4G AP''' | |||
'''WIFI 2.4G AP Guest''' | |||
[[File:Wi-Fi MacID Filtering .png|frameless|620x620px]] | |||
Before adding the MacIDs the user needs to select the mode from the dropdown menu. | |||
In ‘Change Mode’ select one option, | |||
'''Blacklist''' | |||
In blacklist mode, you specify which MAC addresses are not allowed to connect to the wireless network. Devices not on the blacklist will be able to connect. | |||
'''Whitelist''' | |||
In whitelist mode, you specify which MAC addresses are allowed to connect to the wireless network. Devices not on the whitelist will be blocked. | |||
To Add the MacID the user needs to click on Add New option. | |||
[[File:WIFI 2.4G AP Guest.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Status | |||
|Enable/Disable | |||
|Enable or disable the MAC ID filtering. | |||
|- | |||
|2 | |||
|MAC ID | |||
|Example: e8:6f:38:1a:f2:61 | |||
|The MAC address of the device to be whitelisted or blocklisted. | |||
|- | |||
|3 | |||
|Network Name | |||
|Example: WIFI 2.4G AP or Wi-Fi 2.4G AP Guest. | |||
|The network to apply the MAC ID filtering. | |||
|} | |||
Once the required MAC ID and Network Name is configured the user needs to click on the save button to add the details. | |||
The user needs to click on the edit button to do modifications on the pre-existing configuration. | |||
Once the required MACID / Network Name is modified the user needs to click on the save button to reflect the changed value in the application. | |||
=== 5.5 Routing === | |||
In this submodule the user can configure the parameters related to routing of the device like Target address, Networks address etc. Routing configurations allow network packets to be directed between different subnets and networks. | |||
It is further divided into 2 sections, | |||
'''Static IPV4 Routes''' | |||
'''Advanced Static IPV4 Routes''' | |||
'''Static IPV4 Routes:''' | |||
Click on ‘Add’ to add a new interface. | |||
[[File:Static IPV4 Routes.png|frameless|620x620px]] | |||
'''EDIT:''' | |||
To edit the existing device the user needs to click on the edit option. | |||
Once the changes are done click on the save button to save all the changes. | |||
Click on the deleted button to delete the existing device detail. | |||
[[File:Static IPV4 Routes Editing.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Interface | |||
|Ex: eth0.1 | |||
|The network interface to be used for this route. Select the one to use from dropdown. | |||
|- | |||
|2 | |||
|Target | |||
|Ex: 192.168.20.0 | |||
|The destination subnet to which traffic should be routed. | |||
|- | |||
|3 | |||
|IPv4 Netmask | |||
|255.255.255.0 | |||
|The subnet mask for the target network. | |||
|- | |||
|4 | |||
|Metric | |||
|0 | |||
|The priority of the route. | |||
Lower values indicate higher priority. | |||
|- | |||
|5 | |||
|IPv4 Gateway | |||
|Ex: 192.168.10.1 | |||
|The gateway IP address to be used for routing traffic to the target subnet. | |||
|- | |||
|6 | |||
|Route Type | |||
|Unicast | |||
|Standard route for individual destination IP addresses. | |||
Custom changes can be made. | |||
|} | |||
Click on save once configuration changes have been made. | |||
'''Advanced Static IPV4 Routes:''' | |||
Click on ‘Add’ to add a new interface. | |||
[[File:Advanced Static IPV4 Routes.png|frameless|620x620px]] | |||
'''EDIT:''' | |||
To edit the existing device the user needs to click on the edit option. | |||
Once the changes are done click on the save button to save all the changes. | |||
Click on the deleted button to delete the existing device detail. | |||
[[File:Advanced Static IPV4 Routes Editing.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Interface | |||
|Ex: ra0 | |||
|The network interface through which the traffic will be routed. Select as per requirement. | |||
|- | |||
|2 | |||
|To | |||
|Ex: 192.168.10.1 | |||
|This is the target address to which the traffic is being directed. In this case, all traffic destined for 192.168.10.1 will follow this route. | |||
|- | |||
|3 | |||
|IPv4 Netmask | |||
|255.255.255.192 | |||
|This defines the subnet of the destination address. | |||
|- | |||
|4 | |||
|Table | |||
|1.) Local | |||
2.) Main | |||
3.) Default | |||
4.) 220 | |||
5.) custom | |||
|1.) This table contains local routes for the addresses assigned to the local interfaces. It's typically used for host and broadcast addresses. | |||
2.) The primary routing table used by the system. | |||
3.) A fallback table used when no other table is specified. | |||
4.) Often used for policy-based routing. | |||
5.) A user-defined routing table. | |||
|- | |||
|5 | |||
|From | |||
|Ex: 192.168.100.1 | |||
|This source address restricts the route to traffic originating from 192.168.100.1. Traffic from other sources won't use this route. | |||
|- | |||
|6 | |||
|Priority | |||
|20 | |||
|The priority value determines the preference of this route. A lower number means higher priority; 20 is relatively high, so this route will be preferred over routes with higher priority values. | |||
|} | |||
Once all the configurations are done click on the update button to reflect the changes made. | |||
=== 5.6 Others === | |||
In this page the user will get to do all the other miscellaneous configuration with respect to the device based on the required parameters. Each utility serves a specific purpose, providing various functionalities for managing and troubleshooting network configurations and statuses. | |||
[[File:Miscellaneous configuration.png|frameless|620x620px]] | |||
Specification details are given below: | |||
{| class="wikitable" | |||
|SN | |||
|Field Name | |||
|Sample Value | |||
|Description | |||
|- | |||
|1 | |||
|Set Date | |||
|Date and time fields (day, month, year, hour, minute, second) | |||
|Sets the system date and time to the specified values. | |||
|- | |||
|2 | |||
|Get Date | |||
|System | |||
|Retrieves and displays the current system date and time. | |||
|- | |||
|3 | |||
|ipsec status all | |||
|Command ‘Get’ | |||
|Displays the status of all IPsec connections. | |||
|- | |||
|4 | |||
|Wi-Fi Scan | |||
|Command ‘Get’ | |||
|Initiates a scan for available Wi-Fi networks. | |||
|- | |||
|5 | |||
|iPerf3 Client | |||
|IP address (e.g., 192.168.10.100) | |||
|Runs an iPerf3 client to measure network performance. | |||
|- | |||
|6 | |||
|iPerf3 Server | |||
|Command ‘Run’ | |||
|Runs an iPerf3 server to measure network performance. | |||
|- | |||
|7 | |||
|Ping | |||
|IP address or domain (e.g., 8.8.8.8) | |||
|Sends ICMP echo requests to the specified address to check connectivity. | |||
|- | |||
|8 | |||
|traceroute | |||
|IP address or domain (e.g., 8.8.8.8) | |||
|Traces the route packets take to reach the specified address. | |||
|- | |||
|9 | |||
|NTP Sync | |||
|Command ‘Sync’ | |||
|Synchronizes the system time with the configured NTP server. | |||
|- | |||
|10 | |||
|Download Files | |||
|File or database identifier | |||
|Initiates a download of the specified file or database. | |||
|- | |||
|11 | |||
|Restart Power | |||
|Command ‘Restart’ | |||
|Restarts the power of the device. | |||
|- | |||
|12 | |||
|Restart Modem | |||
|Command ‘Restart’ | |||
|Restarts the modem. | |||
|- | |||
|13 | |||
|Run AT Command | |||
|Enter AT command | |||
|Executes the specified AT command on the modem. | |||
|- | |||
|14 | |||
|Show Board Configuration | |||
|Command ‘Show’ | |||
|Displays the current board configuration. | |||
|- | |||
|15 | |||
|Show VPN Certificate Name | |||
|Command ‘Show’ | |||
|Displays the name of the VPN certificate in use. | |||
|- | |||
|16 | |||
|Switch SIM to Secondary (Takes >2 mins) | |||
|Command ‘Run’ | |||
|Switches the active SIM to the secondary SIM card. | |||
|- | |||
|17 | |||
|Send test SMS | |||
|Phone number (e.g., +911234567890) message text (e.g., "Hello how are you?") | |||
|Sends a test SMS to the specified phone number. | |||
|- | |||
|18 | |||
|ReadlatestSMS | |||
|Command ‘Read’ | |||
|Reads the most recent SMS received by the device. | |||
|- | |||
|19 | |||
|Data Usage | |||
|'''From:''' Start date (YYYY-MM-DD) | |||
'''To:''' End date (YYYY-MM-DD) | |||
|Displays data usage statistics for the specified date range. | |||
|- | |||
|20 | |||
|Monthly Data Usage | |||
|'''Month:''' Month (e.g., 07) | |||
'''Year:''' Year (e.g., 2024) | |||
|Displays data usage statistics for the specified month and year. | |||
|- | |||
| | |||
| | |||
| | |||
| | |||
|- | |||
|21 | |||
|Modem Debug Info | |||
|Command ‘Read’ | |||
|Displays debug information for the modem. | |||
|- | |||
|22 | |||
|Scan Network operators (Takes >3 mins) | |||
|Command ‘Scan’ | |||
|Initiates a scan for available network operators. | |||
|- | |||
|23 | |||
|Network operator list (First Perform Scan Network Operators) | |||
|Command ‘Show’ | |||
|Displays the list of network operators detected in the previous scan. | |||
|- | |||
|24 | |||
|ReadLogFiles | |||
|Log file identifier | |||
|Reads and displays the specified log file | |||
|- | |||
|25 | |||
|Enable ssh (Admin) | |||
|Command ‘Run’ | |||
|Enables SSH access for the admin user. | |||
|- | |||
|26 | |||
|Disable ssh (Admin) | |||
|Command ‘Run’ | |||
|Disables SSH access for the admin user. | |||
|- | |||
|27 | |||
|ClearSIM1Data | |||
|Command ‘Clear’ | |||
|Clears data usage statistics for SIM1. | |||
|- | |||
|28 | |||
|ClearSIM2Data | |||
|Command ‘Clear’ | |||
|Clears data usage statistics for SIM2. | |||
|- | |||
|29 | |||
|Create Bridge with SW_LAN | |||
|Network interface identifier | |||
|Creates a network bridge with the specified interface and SW_LAN. | |||
|- | |||
|30 | |||
|Show Bridge | |||
|Command ‘Show’ | |||
|Displays information about the current network bridges. | |||
|- | |||
|31 | |||
|Delete Bridge | |||
|Command ‘Delete’ | |||
|Deletes the specified network bridge. | |||
|- | |||
|32 | |||
|Output | |||
|Any value | |||
|Displays output for all the above actions. | |||
|} | |||
= 6.Logout = | |||
The user should click on log out option to logged out from the router application. | |||
[[File:Logout.png|frameless|620x620px]] | |||
Latest revision as of 12:57, 7 August 2024
Connecting with the device to the System (Laptop/Desktop)
To log in to SILBO_IA44-A by connecting the router to your laptop or desktop via LAN or using Wi-Fi, please follow the steps below.
Connecting via LAN:
Connect your laptop's LAN port to one of the router's LAN interfaces. Ensure that you select any LAN interface (there is one available) while making sure the WAN interface is not used.
How to connect with the SILBO_IA44-A application
Once the LAN connection is established between the device and the laptop or the desktop
Please open the command prompt and ping to get the IP config of that device.
Type the command Ipconfig
It will provide the Ip address/url of that device through which the application can be accessed.
Log In
Open the web browser and type the IP address in the URL.
It will show the log in page of the application.
Give the valid credentials for the username and password to login to the application page.
Once the user credentials are provided it will direct to the landing page of the application.
The “Status” landing page shows all the detailed specification of the device like system, memory storage and connection tracking etc.
The application is divided in to 8 Modules.
- Info
- Settings
- Maintenance
- Status
- Features
- Logout
1. Info
The “Info” module provides the information about the devices to the user.
It provides all the specification related to the hardware, firmware, Networks and the Connection uptimes.
It has 3 submodules.
- Overview
- System Log
- Kernel Log
1.1 Overview
In overview module it displays all the specification categorically of a device like System, Memory, storage, Connection tracking, DHCP Lease.
System:
In this section it displays the hardware configured specification of the device.
The specifications details are as follows,
| SN | Field name | Sample value | Description |
| 1 | Hostname | 37A26230014 | This field displays the router serial number of the device |
| 2 | Model | Silbo_IA44-A- EC200A | This field displays the model number of the device |
| 3 | Firmware Version and IPK Version | 1.16_1.13_RC4 | This field displays the firmware version and IPK version |
| 4 | Kernel Version | 4.14.180 | This field displays the kernel version of the device |
| 5 | Local Time | Monday, July 1, 2024, at 05:43:58 PM | This field displays the local time |
| 6 | Uptime | 0h 7m 29s | This field displays the uptime of the device |
| 7 | Load Average | 1.73 1.87 1.04 | This field displays the average load |
Memory:
In this section it displays the memory configured specification of the device.
The specifications details are as follows.
| SN | Field name | Sample value | Description |
| 1 | Total Available | 68676 kB / 124208 kB (55%) | This field displays the total availability of memory space in the device |
| 2 | Free | 59344 kB / 124208 kB (47%) | This field displays the Free memory space in the device |
| 3 | Cached | 312 kB / 124208 kB (0%) | This field displays the Cached memory space in the device |
| 4 | Buffered | 9332 kB / 124208 kB (7%) | This field displays the Buffered memory space in the device |
Storage:
In this section it displays the status of storage as root and temporary usage specification of the device.
The specifications details are as follows.
| SN | Field name | Sample value | Description |
| 1 | Root Usage | 796 kB / 15488 kB (5%) | This field displays the total root usage of the device |
| 2 | Temporary Usage | 312 kB / 62104 kB (0%) | This field displays the total temporary usage of the device |
Connection Tracking:
In this section it displays the status of connection tracking for the device.
The specifications details are as follows.
| SN | Field Value | Sample Value | Description |
| 1 | Active Connections | 48/16384 (0%) | This field displays the active connection of the device. |
DHCP Leases:
In this section it displays the DHCP lease of the temporary assignment of an IP address to a device on the network.
The specifications details are below.
| SN | Field name | Sample value | Description |
| 1 | Host Name | KermaniK-LT | This field displays the configured Host Name/Username for that device. |
| 2 | IPv4-Address | 192.168.10.147 | This field displays the IP address of the device. |
| 3 | MAC-Address | 34:73:5a:bb: ab:7a | This field displays the MAC-Address of the device. |
| 4 | Lease time remaining | 11h 53m 49s | This field displays the lease time remaining for the device. |
1.2 System Log
This page provides on screen System logging information. In this page the user gets to view the system logs.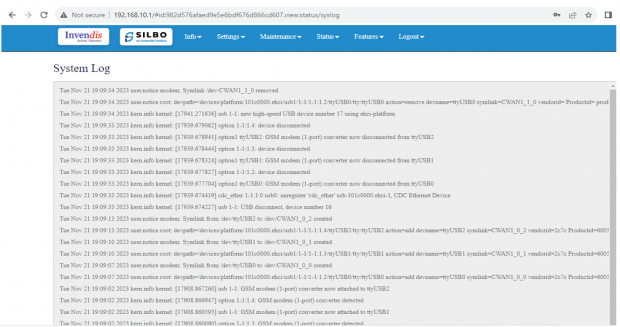
1.3 Kernel Log
This page provides on screen Kernel logging information.
In this page the user gets to view the Kernel logs.
2. Setting
In this “Setting” module the user can Configure/update all the required parameters related to Network, SIM Switch, Internet, VPN, Firewall, Loopback Rule, Remote monitoring, Tunnel as per requirement.
IT consist of 8 submodules.
- Network
- Sim Switch
- Internet
- VPN
- Firewall
- Loopback Rule
- Remote Monitoring
- Tunnel
2.1 Network
In this section the user does all the setting related configuration with reference to network like Ethernet Setting, Cellular Setting, Band lock and Operator Lock, Wi-Fi, Guest Wi-Fi, Wireless Schedule, SMS Setting, Loopback IP.
Ethernet Setting:
In this page it will display all the configured port that is attached with the device.
For this device 2 ports are configured. Ethernet mode can be configured as WAN and as LAN as well. Ethernet LAN Connection settings can be configured as DHCP server or Static.
For port 2 settings,
Kindly select the option LAN for Port 2 mode LAN/WAN. Based on the option selected the field will also change. The user needs to configure all the required field and click on the save to save the required fields.
| SN | Field name | Sample value | Description |
| 1 | Port 2 mode LAN/WAN | LAN | This field displays the port mode selection |
| 2 | Port 2 Ethernet Protocol [LAN Eth0.1] | DHCP Server | This field displays the Ethernet mode selection |
| 3 | Port 2 DHCP Server IP | 192.168.10.1 | This field displays DHCP server IP configured. |
| 4 | Port 2 DHCP Netmask | 255.255.255.0 | This field displays DHCP server Netmask address configured |
| 5 | Port 2 DHCP Start Address | 100 | This field displays DHCP server start address configured |
| 6 | Port 2 DHCP Limit | 50 | This field displays DHCP server limit |
| 7 | Port 2 Internet Over LAN | Enable | Enabling this option allows devices connected to Port 2 to access the internet through the LAN. |
| 8 | DNS Server | 1/2 | This setting typically indicates that one or two DNS server is configured. |
| 9 | DNS Server Address | Ex: 8.8.8.8 | This is the IP address of the DNS server that the devices on your network will use for DNS queries. |
Kindly select the option EWAN for Port 2 mode LAN/WAN. Based on the option selected the field will also change. The user needs to configure all the required field and click on the save to save the required fields.
The specifications details are below.
| SN | Field name | Sample value | Description |
| 1 | Port 2 mode LAN/WAN | EWAN | This field displays the port mode selection |
| 2 | Ethernet Protocol Port 2 WAN | DHCP client | This field displays the client |
| 3 | Gateway | 192.168.1.1 | This field displays gateway address configured |
Click on the save once all the configuration is done and click on the update button to update all the information.
SW_LAN settings,
In this part the user can configure the setting for SW_LAN.
Note: After any changes made, save and update the page below.
The specifications details are below.
| SN | Field name | Sample value | Description |
| 1 | SW_LAN Ethernet Protocol | DHCP Server | This field displays the Ethernet mode selection. |
| 2 | SW_LAN DHCP Server IP | 192.168.10.1 | This field displays DHCP server IP configured which can be changed accordingly. |
| 3 | SW_LAN DHCP Netmask | 255.255.255.0 | This field displays DHCP server Netmask address configured. |
| 4 | SW_LAN DHCP Start Address | 100 | This field displays DHCP server start address configured. |
| 5 | SW_LAN DHCP Limit | 50 | This field displays DHCP server limit. |
| 6 | DNS Server | 1 | This filed display number of DNS server availability. |
| 7 | DNS Server Address | 8.8.8.8 | This filed display the DNS server address. |
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information.
Static option for SW_LAN Ethernet Protocol:
Select the option of static from the drop-down menu for SW_LAN Ethernet Protocol.
Note: After any changes made, save and update the page below.
The specifications details are below.
| SN | Field name | Sample value | Description |
| 1 | SW_LAN Ethernet Protocol | Static | This field displays the Ethernet mode selection |
| 2 | SW_LAN static IP | 192.168.5.1 | This field displays static server IP configured. |
| 3 | SW_LAN Netmask | 255.255.255.0 | This field displays static server Netmask address configured |
| 4 | DNS Server | 1 | This filed display number of DSN server availability |
| 5 | DSN Server Address | 8.8.8.8 | This filed display the DSN server address. |
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information.
Cellular Setting:
In this page, the user needs to configure the various details with respect to the SIM.
Select single cellular single sim where the user must configure the APN details of the sim used for the router device. The Configurations can be done based on the SIM usage, with respect to IPV4 or IPV6.
The specifications details are below.
| SN | Field name | Sample value | Description |
| 1 | Cellular Enable | Checkbox | Check this box to enable cellular functionality. |
| 2 | Cellular Operation Mode | 1.) Single Cellular with Dual Sim
2.) Single Cellular with Single SIM |
1.) This mode allows you to use one cellular modem with two SIM cards.
2.) This mode allows you to use one cellular modem with single SIM card. |
| 3 | Cellular Modem 1 | QuectelEC200A | This field displays the modem name. |
| 4 | Choose SIM 1 APN Mode | 1.) Auto
2.) Manual |
1.) Choose Auto for regular SIM to detect APN name automatically.
2.) Choose manual to enter the APN settings manually in case of M2M SIM cards. |
| 5 | SIM 1 Access Point Name | airtelgprs.com | Enter the APN provided by your cellular service provider in case of M2M sim. For regular sim cards APN name will be displayed automatically. |
| 6 | SIM 1 PDP Type | IPV4 | Choose the PDP type, which is typically either IPv4 or IPv6 depending on the sim card. |
| 7 | SIM 1 Username | Enter the username if required by the APN. Leave blank if not required. | |
| 8 | SIM 1 Password | Enter the password if required by the APN. Leave blank if not required. | |
| 9 | SIM 1 Authentication Protocol | None | Choose the authentication protocol. Options typically include None, PAP, or CHAP. |
| 10 | Choose SIM 2 APN Mode | 1.) Auto
2.) Manual |
1.) Choose Auto for regular SIM to detect APN name automatically.
2.) Choose manual to enter the APN settings manually in case of M2M SIM cards. |
| 11 | SIM 2 Access Point Name | airtelgprs.com | Enter the APN provided by your cellular service provider in case of M2M sim. For regular sim cards APN name will be displayed automatically. |
| 12 | SIM 2 PDP Type | IPV4 | Choose the PDP type, which is typically either IPv4 or IPv6 depending on the sim card. |
| 13 | SIM 2 Username | Enter the username if required by the APN. Leave blank if not required. | |
| 14 | SIM 2 Password | Enter the password if required by the APN. Leave blank if not required. | |
| 15 | SIM 2 Authentication Protocol | None | Choose the authentication protocol. Options typically include None, PAP, or CHAP. |
| 16 | Primary SIM Switchback Time (In Minutes) | 10 | Enter the time in minutes after which the system should switch back to the primary SIM if it becomes available. |
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information.
Band lock and Operator Lock:
In this page, the user needs to configure the lock band and operator based on the service provider.
Bands available in the drop-down list.
2G/3G option:
2G/3G: - 3G allows additional features such as mobile internet access, video calls and mobile TV. While the main function of 2G technology is the transmission of information through voice calls.
The user should select the band check box available for 2g/3g from the given list. Bands available for selection under LTE for the bands available in that area.
Operator Selection Mode:
The user needs to click on the check box of the “operator select enable” to select the operator.
Once the check box is clicked there will be a dropdown list of the operator modes from which the user needs to select the mode. The user needs to select the operator mode from the given dropdown list.
If the user selects the mode “Manual” or “Manual-Automatic” then one more text box will appear where the user must provide the operator code.
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information.
Wi-Fi Setting:
In this, router has the general setting and change country code, channel, radio mode, radio passphrase as per the requirement after clicking on enable Radio button.
The user needs to select the respective radio mode based on its need.
It has 3 radio modes.
‘Access point’, ‘client only’ and ‘Access point and client’
Refer the below picture.
Access Point mode:
In Access Point mode, a configuration in which a router, allows wireless devices to connect to a wired network by creating a Wi-Fi hotspot.
Client point:
In client mode, the access point connects your wired devices to a wireless network. This mode is suitable when you have a wired device with an Ethernet port and no wireless capability, for example, a smart TV, Media Player, or Game console and you want to connect it to the internet wirelessly, select the Client Mode and give the Radio SSID & client passphrase.
Access point and client point:
Select this option for both type of connection, give both SSID and passphrase.
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information.
The specifications details are below.
| SN | Field name | Sample value | Description |
| 1 | Radio 0 Protocol | IEEE 802.11 b/g/n | This section shows the radio protocol which is by default. |
| 2 | Country Code | INDIA | Select the country accordingly.
(INDIA by default) |
| 3 | Channel | Auto | In this dropdown the user should select the proper channel to be used. (Auto by default) |
| 4 | TX Power | 100 | In this text box the user should specify the power. |
| 5 | Channel Width | 20 MHz | In this dropdown the user should select the channel width |
| 6 | Radio Mode | 1.) Access point
2.) Client only 3.) Access point and client |
In this drop down the user should select the mode.
(Access point by default) |
| 7 | Radio SSID | AP_37A26230014 | In this text box the user should specify the SSID number which usually comes with the router. |
| 8 | Radio Authentication | WPA2 Personal (PSK) | In this dropdown the user should select the type of authentication.
(WPA2 Personal (PSK) by default) |
| 9 | Radio Encryption | AES | In this dropdown the user should select the type of encryption required.
(AES by default) |
| 10 | Radio Passphrase | ********* | In this text box the user should specify the password. Password will be given with the router which can be changed later. |
| 11 | Radio DHCP server IP | 192.168.100.1 | In this text box the user should specify the IP address of DHCP server.
(192.168.100.1 will be default which can be changed accordingly) |
| 12 | Radio DHCP start address | 100 | In this text box the user should specify the start address of the DHCP.
(100 value is default) |
| 13 | Radio DHCP limit | 50 | In this text box the user should specify the limit for the DHCP.
(50 value is default) |
Wireless Schedule:
Wi-Fi can be automatically withdrawn based on the configuration done in this section.
The user can schedule the Wi-Fi’s accessibility time during a particular period.
After configuring all the required information, the user should click on save and then click on update to update all the required information.
The user can select more than one “day of the week” for scheduling the Wi-Fi working hours.
Loop back IP settings:
The loopback IP address, often referred to as “localhost.” it is used to establish network connections within the same device for testing and troubleshooting purpose.
The loopback IP address, commonly represented as 127.0.0.1, is a special address used for testing network connectivity on a local machine.
It allows a device to send network messages to itself without involving external networks, making it useful for troubleshooting and diagnostics.
However, this IP can be changed as per requirement and to do that, Navigating to Setting>>Network configuration>> Loopback IP settings can be changed/updated.
After configuring all the required information, the user should click on the save and then click on the update to update the all the required information.
The loopback IP address, commonly represented as 127.0.0.1, is a special address used for testing network connectivity on a local machine. It allows a device to send network messages to itself without involving external networks, making it useful for troubleshooting and diagnostics.
However, this IP can be changed as per requirement and to do that, Navigating to Setting>>Network configuration>> Loopback IP settings can be changed/updated.
SMS Settings:
User needs to enable SMS option in SMS settings page.
This option is to validate the mobile numbers using which controlling commands could be sent to the router device.
1 to 5 mobile numbers can be authenticated by choosing from “Select Valid SMS user numbers” and adding the mobile numbers below respectively.
API key is the pass key used in the commands while sending SMS.
Displayed in the below screen is the default API key which can be edited and changed as per choice. After addition of the mobile number’s user needs to click on save button for changes to take place.
1.) Select valid user number max. 5 and add authorized phone number in the tab where you want to find the alert and click on ‘SMS Response Enable’, ‘save’ and ‘update’ button.
2.) Now send SMS commands from the configured mobile number.
3.) Once the commands are received from the user phone number the board will send acknowledgement as per the commands.
4.) After that it will send the router’s status once it has rebooted and is operational again.
Mentioned below are a few commands which can be sent from the configured mobile number to the router device. Below two commands are One for rebooting the router device and another to get the uptime.
1) {"device”: ["passkey”, “API key"],"command":"reboot","arguments":"hardware"}
2) {"device”: ["passkey ","API key"],"command”: “uptime"}
After configuring all the required information, the user should click on save and then click on update to update all the required information.
2.2 SIM Switch
In this page the user needs to configure the Sim for the given device.
The user needs to select from the drop-down menu on which basis the sim needs to be switched.
Once the user selects on “signal strength” then the parameters related to signal strength will pop up and the user needs to configure the parameters based on the requirement.
Threshold RSRP:
This Needs to be set appropriately. Incorrect setting may cause unnecessary SIM switching. (In General, a BAD RSRP value range is -140 to -115 and FAIR RSRP value range is -115 to -105).
Threshold SINR:
This Needs to be set appropriately. Incorrect setting may cause unnecessary SIM switching. (In General, a BAD SNR value range is -20 to 0 and FAIR SNR value range is 0 to 13)
Once the user selects on “Data Limit” then the parameters related to Data Limit will pop up and the user needs to configure the parameters based on the requirement.
| SN | Field name | Sample value | Description |
| 1 | SIM Switch Based on | Data Limit | The user needs to select from the drop-down menu on what basis the sim needs to be switched. |
| 2 | SIM 1 Data Usage Limit (In MB) | 1000 | The user needs to set the limit for the data usage for SIM 1. |
| 3 | SIM 2 Data Usage Limit (In MB) | 1000 | The user needs to set the limit for the data usage for SIM 2. |
| 4 | Periodicity | Daily | The user needs to set the pattern/frequency to switch the sims. |
| 5 | Day Of Month | 16 | The user needs to set the day for switching the sim. |
2.3 Internet
In this page the user needs to configure the internet connection to set the priority from the diverse options. The user should decide what kind of connection it needs to provide to the device like LAN, WAN etc. Once the connections are configured then click on save option and then on update.
If the user needs to edit on the existing configuration, then the user should click on the “EDIT” button.
The specifications details are below.
| SN | Field name | Sample value | Description |
| 1 | Name | EWAN2 | This field displays the name of the WAN connection |
| 2 | Priority | 1 | In this dropdown box the user needs to select the priority. |
| 3 | Select Track IP Numbers | 2 | In this dropdown the user needs to select the track number for the Ips. This specifies the number of IP addresses that will be used for tracking the status of the connection. |
| 4 | TrackIP1 | 8.8.8.8 | This is the first IP address used for tracking the connection. 8.8.8.8 is a public DNS server provided by Google.
|
| 5 | TrackIP2 | 8.8.4.4 | This is the second IP address used for tracking the connection. 8.8.4.4 is another public DNS server provided by Google.
|
| 6 | Reliability | 1 | This indicates the reliability threshold for considering the connection as up. A value of 1 typically means that only one successful ping response is needed to deem the connection reliable.
|
| 7 | Count | 1 | This specifies the number of consecutive pings sent to the track IP addresses. |
| 8 | Up | 1 | This indicates the number of successful pings required to consider the connection as up. |
| 9 | Down | 1 | This indicates the number of failed pings required to consider the connection as down. |
Once the user is done with modification click on the save button to save all the changes and then click on the update button.
2.4 VPN
VPN stands for Virtual Private Network, it establishes a connection between the system and a remote server, which is owned by a VPN provider.
Creating a point-to-point tunnel that encrypts the personal data, masks the IP address, and allows to block the required website to blocks via firewalls on the internet.
Navigate to settings >= VPN, general settings and you will see all VPN options you wish to use.
Refer the below figure.
There are 5 types of setting available under VPN configuration.
- General Settings
- IPSEC
- Open VPN
- Wireguard
- Zerotier
General Settings:
In this page the user must choose which type of VPN connection is required for the device. The user must select from IPSEC, Open VPN, Wireguard or Zerotier based on its requirement. If required, the user can select all the options. The user needs to click on the save after selecting the option based on its use.
IPSEC:
IPSEC VPN is used to create a VPN connection between local and remote networks.
To use IPSEC VPN, the user should check that both local and remote routers support IPSEC VPN feature.
In this page the user can add/edit/delete the IPSEC VPN connection for the device.
The user needs to click on the update button once the required configuration is completed.
In IPSEC the user needs to click on edit button to edit the configuration of an existing VPN connection.
Click on update once done with configurations.
The tunnel will show established, showing the connection has been made.
Detailed specifications are below:
| SN | Field name | Sample value | Description |
| 1 | IPSEC | Site to Site VPN | In this dropdown the user should select the IPSEC connection type. |
| 2 | IPSEC Role | Client/Server | In this dropdown box the user needs to select the IPSEC role. The device is acting as a client in the VPN setup (in this example). |
| 3 | Connection Type | Tunnel | In this dropdown the user needs to select the connection type. The user should select on the connection enable check box. |
| 4 | Connection mode | Route/add/start/trap | In this drop down list the user should select the mode for the connection. In this example start is selected which means the VPN connection is initiated automatically. |
| 5 | Remote Server IP | ******** | The IP address of the remote VPN server. |
| 6 | Local ID | 3.3.3.3 | The user needs to set the local id. It is the identification for the local VPN client. |
| 7 | No. of local subnets | 1 | In this dropdown the user needs to select how many subnets will be connected. |
| 8 | Local Subnet 1 | 172.16.31.25/32 | In this text box the user needs to put the specific local subnet included in the VPN. |
| 9 | Remote id | 1.1.1.1 | In this text box the user needs to put the id of the remote connection. It is the identification for the remote VPN server. |
| 10 | No of remote subnet | 1 | In this dropdown the user needs to select how many subnets it will be connected remotely. |
| 11 | Remote subnet | 10.1.1.0/24 | In this text box the user needs to put the address of the remote subnet. The specific remote subnet included in the VPN. |
| 12 | Key exchange | Ikev1 | In this dropdown the user should select the which key exchange version to be selected. |
| 13 | Aggressive | Yes/No | In this dropdown the user should select either yes or no. |
| 14 | IKE Lifetime (In Seconds) | 86400 | The lifetime of the IKE phase in seconds (1 day). |
| 15 | Lifetime (in seconds) | 28800 | The lifetime of the IPsec SA (Security Association) in seconds (8 hours). |
| 16 | Enable DPD Detection | 1
0 |
Indicates whether Dead Peer Detection is enabled to detect a lost connection. Enable this option as per server-side settings. |
| 17 | Time Interval (In Seconds) | 60 | This option is available only if DPD Detection is enabled. The time interval is the interval for DPD checks. |
| 18 | Action | Restart/clear/hold/
trap/start |
Restart: Action to take when DPD detects a lost connection (restart the connection). Select as per server-side setting. |
| 19 | Authentication Method | PSK | PSK: Pre-shared key is used for authentication. Select this option for authentication as per sever side setting. |
| 20 | Multiple Secrets | 1/0 | Indicates whether multiple PSK secrets are used. Enable only if required. |
| 21 | PSK Value | ****** | Pre-shared key value (masked for security). |
| Proposal settings Phase I | ||||||
| 22 | Encryption Algorithm | AES 128
AES 192 AES 256 3DES |
AES 256: Encryption algorithm for Phase I. Select as per server-side configuration. Both server and client should have same configuration. | |||
| 23 | Authentication Phase I | SHA1
MD5 SHA 256 SHA 384 SHA 512 |
SHA 512: Authentication algorithm for Phase I.
Select as per server-side configuration. Both server and client should have same configuration. | |||
| 24 | DH Group | MODP768(group1)
MODP1024(group2) MODP1536(group5) MODP2048(group14) MODP3072(group15) MODP4096(group16) |
MODP2048 (group14): Diffie-Hellman group for key exchange.
Select as per server-side configuration. Both server and client should have same configuration. | |||
| Proposal settings Phase II | ||||||
| 25 | Hash Algorithm | AES 128
AES 192 AES 256 3DES |
AES 256: Encryption algorithm for Phase II. Select as per server-side configuration. Both server and client should have same configuration. | |||
| 26 | Authentication Phase II | SHA1
MD5 SHA 256 SHA 384 SHA 512 |
SHA 512: Authentication algorithm for Phase II.
Select as per server-side configuration. Both server and client should have same configuration. | |||
| 27 | PFS Group | MODP768(group1)
MODP1024(group2) MODP1536(group5) MODP2048(group14) MODP3072(group15) MODP4096(group16) |
MODP2048 (group14): Perfect Forward Secrecy group.
Select as per server-side configuration. Both server and client should have same configuration. | |||
Open VPN:
In the OpenVPN connection, the home network can function as a server, and the remote device can access the server through the router which acts as an OpenVPN Server gateway.
To use the VPN feature, the user should enable OpenVPN Server on the router, and install and run VPN client software on the remote device.
The user needs to “upload” the respective certificate from a valid path and then click on the “Update.”
Once the OpenVPN connection starts the user will get an option to enable/disable the VPN connection as and when required.
By clicking on the enable/disable button, the user can start/stop the VPN connection.
VPN has been established.
WireGuard:
WireGuard is simple, fast, lean, and modern VPN that utilizes secure and trusted cryptography.
Click on “Edit” to start configurations as needed.
EDIT:
Click on the save button after the required configuration.
| SN | Field name | Sample value | Description |
| 1 | Wireguard Role | Client/Server | In this dropdown box the user needs to select the wireguard role. |
| 2 | Listen Port | 51820 | The UDP port on which the WireGuard client listens for incoming connections. |
| 3 | IP Addresses | 10.0.0.1/24 | The IP address and subnet mask assigned to the WireGuard client's interface. This address is used within the VPN. |
| 4 | Allowed PeerIPs | 10.1.1.1 | The IP address of the allowed peer(s) that can connect to this WireGuard client. This might need adjustment based on the actual peer IPs used in the network. |
| 5 | Endpoint HostIP | 10.1.1.1 | The IP address of the WireGuard server (the endpoint to which the client connects). |
| 6 | Endpoint HostPort | 51820 | The port on the WireGuard server to which the client connects. |
| 7 | PeerPublicKey | ***** | The public key of the peer (the server) the client is connecting to. This key is part of the public-private key pair used in WireGuard for encryption and authentication. |
| 8 | Enable Preshared key | Yes/No | This option indicates that a pre-shared key (PSK) is used in addition to the public-private key pair for an extra layer of security. |
| 9 | Preshared key | ***** | The actual pre-shared key value shared between the client and the server. This option appears only if you have enabled preshared key. |
Zerotier:
ZeroTier is a tool that lets you create your own private network over the internet.
Go to ZeroTier Central and sign up for a free account. In ZeroTier Central, click on "Create a Network". This will generate a unique 16-digit network ID for your new network.
Go to settings => VPN, in general settings, enable ZeroTier and save.
Copy and paste the unique 16-digit network ID in the edit section.
Click on the save button after the required configuration.
| SN | Field name | Sample value | Description |
| 1 | NetworkID | Ad2769hfkw2345f4 | In this dropdown box the user needs to paste the unique 16-digit network id. |
| 2 | Listen Port | 9993 | Default |
2.5 Firewall
A firewall is a layer of security between the network and the Internet. Since a router is the main connection from a network to the Internet, the firewall function is merged into this device. Every network should have a firewall to protect its privacy.
There are 6 types of setting available under firewall.
- General Settings
- Port forwards
- Traffic Rules
- SNAT traffic Rules
- Parental Control
- Zone Forwarding
General Settings:
General settings are subdivided into 2 parts,
1.) General settings
In general settings, the settings that are made are default settings and can be changed according to user’s preference.
| SN | Field Name | Sample Value | Description |
| 1 | Enable SYN-flood protection | Enabled | This is enabled by default; setting can be changed if required. |
| 2 | Disable IPV6 | Disabled | This is enabled by default; setting can be changed if required. |
| 3 | Drop invalid packets | Disabled | This is enabled by default; setting can be changed if required. |
| 4 | TCP SYN Cookies | Disabled | This is enabled by default; setting can be changed if required. |
| 5 | Input | Reject/Accept | By default, the setting is ‘Reject’ but this needs to be changed to ‘Accept’ compulsory. |
| 6 | Output | Reject/Accept | By default, the setting is ‘Reject’ but this needs to be changed to ‘Accept’ compulsory. |
| 7 | Forward | Reject/Accept | By default, the setting is ‘Reject’ but this needs to be changed to ‘Accept’ compulsory. |
2.) Zone settings
In zone settings, there’s an option to add “New Zone”, according to user’s requirement.
Port Forwards:
Port forwarding is a feature in a router or gateway that allows external devices to access services on a private network.
It maps an external port on the router to an internal IP address and port on the local network, enabling applications such as gaming servers, web servers, or remote desktop connections to be accessed from outside the network.
This helps in directing incoming traffic to the correct device within a local network based on the port number, enhancing connectivity and accessibility.
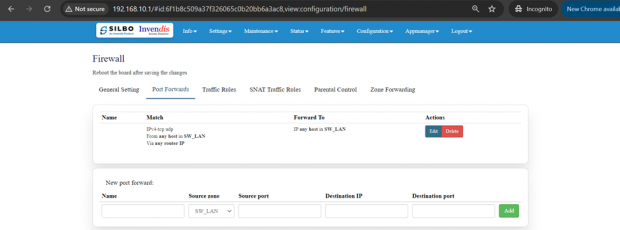
EDIT:
Click on the save button after the required configuration.
| SN | Field name | Sample value | Description |
| 1 | Name | Example: Web_Server_Forward
|
Field must not be empty. Provide a name for the rule to easily identify it. |
| 2 | Protocol | Example: TCP+UDP
|
Select the protocol for the rule.
Options typically include TCP+UDP, TCP, UDP, ICMP, Custom. |
| 3 | Source zone | Example: SW_LAN
|
Select the source zone where the traffic is originating from. Options typically include EWAN2,SW_LAN,CWAN1,CWAN1_0,CWAN1_1,VPN |
| 4 | Source MAC address [optional] | Example: any
|
any: Leave as any if you don't want to specify a MAC address.
|
| 5 | Source IP address[optional] | Example: Leave blank if not needed. | Optionally specify an IP address or range. |
| 6 | Source port | Example: 80, 443 (if matching traffic for web server ports)
|
Specify the source port or port range. |
| 7 | Destination zone | Example: SW_LAN
|
Select the destination zone where the traffic is heading to. |
| 8 | Destination IP address | Leave blank if not needed. | Optionally specify the destination IP address or range. |
| 9 | Destination port | Example: 80 (if redirecting to a web server port)
|
Specify the destination port or port range. |
Traffic Rule:
"Traffic rules" refer to the policies and regulations that govern the flow of data packets within a network.
To allow new traffic, click on “Add and Edit” in “New Traffic Rule”.
EDIT:
| SN | Field name | Sample value | Description |
| 1 | Name | Example: Allow_HTTP_and_HTTPS | Field must not be empty: Provide a descriptive name for the traffic rule. |
| 2 | Restrict to Address Family | 1. Options: IPv4, IPv6
Example: IPv4 if dealing with typical internet traffic. |
Select the address family to generate iptables rules for. |
| 3 | Protocol | Example: TCP+UDP | TCP+UDP: Match incoming traffic using the given protocol. |
| 4 | Match ICMP Type | Example: any | Match all ICMP types if set to any. Specific types can be chosen if needed. |
| 5 | Source Zone | Example: LAN | Specifies the traffic source zone. |
| 6 | Enable DDoS Prevention | Example: ‘Checked’ if you want to enable DDoS prevention measures | Enable or disable Distributed Denial of Service (DDoS) prevention. |
| 7 | Source MAC Address | Example: any | any: Match traffic from any MAC address or specify a particular MAC address. |
| 8 | Source Address | Example: 192.168.1.0/24 | Match incoming traffic from the specified source IP address or range. |
| 9 | Source Port | Example: any if all source ports should be matched | any: Match incoming traffic from the specified source port or port range. |
| 10 | Destination Zone | Example: WAN | Specifies the traffic destination zone. |
| 11 | Action | Example: ACCEPT | Options: ACCEPT, DROP, REJECT. Specify the action to take for matched traffic. |
| 12 | Limit | Example: 10/minute to limit matches to 10 times per minute. | Maximum average matching rate; specified as a number, with an optional /second, /minute, /hour, or /day suffix. |
| 13 | Extra arguments | Example: --log-prefix "Blocked: " to add a log prefix to log messages for this rule. | Passes additional arguments to iptables. Use with care as it can significantly alter rule behaviour. |
Click on save once configured.
SNAT Traffic Rule:
For configuring SNAT (Source Network Address Translation) traffic rules, you can control how outbound traffic from your local network is translated to a different IP address as it exits the network.
To add new source NAT,
Click on “ADD” in “New Source NAT:”
EDIT:
Specification details are below:
| SN | Field name | Sample value | Description |
| 1 | Name | Example: SNAT_WAN_to_LAN | Field must not be empty: Provide a unique and descriptive name for the SNAT rule. |
| 2 | Protocol | Example: TCP+UDP | TCP+UDP: Select the protocols that the SNAT rule will apply to. |
| 3 | Source Zone | Example: wan | wan: Specifies the source zone from which the traffic originates. |
| 4 | Source IP Address | Example: any or a specific range like 192.168.1.0/24 | -- please choose --: Specify the source IP address or range. Leave empty if the rule applies to any source IP. |
| 5 | Source Port | Example: any | any: Specify the source port or port range from which the traffic originates. |
| 6 | Destination Zone | Example: lan | lan: Specifies the destination zone to which the traffic is directed. |
| 7 | Destination IP Address | Example: any or a specific IP like 192.168.1.100 | -- please choose --: Specify the destination IP address or range. Leave empty if the rule applies to any destination IP. |
| 8 | Destination port | Example: any | any: Specify the destination port or port range to which the traffic is directed. |
| 9 | SNAT IP Address | Example: 203.0.113.5 (an external IP address) | -- please choose --: Specify the IP address to which the source IP should be translated. |
| 10 | SNAT Port | Example: Leave empty if not needed, or specify a port like ‘12345’ | Optionally, rewrite matched traffic to a specific source port. Leave empty to only rewrite the IP address. |
| 11 | Extra Arguments | Example: --log-prefix "SNAT_traffic: " (to add a log prefix to log messages for this rule) | Pass additional arguments to iptables. Use with care as it can significantly alter rule behaviour. |
Click on save once configured.
Parental Control:
For configuring parental control rules, you want to set restrictions based on time, source, and
destination zones, as well as specific devices.
To add parental control in firewall,
Click on “Add and Edit” in “New parental control:” field.
EDIT:
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Name | Example: Parental_Control_Sunday | Field must not be empty: Provide a unique and descriptive name for the parental control rule. |
| 2 | Proto | all | all: This specifies that the rule will apply to all protocols. |
| 3 | Source Zone | Example: lan | Field must not be empty: Please look at Firewall->Zone Settings to find zone names. |
| 4 | Destination Zone | Example: wan | Field must not be empty: Please look at Firewall->Zone Settings to find zone names. |
| 5 | Source MAC Address | Example: 00:1A:2B:3C:4D:5E | Field: Enter the MAC address of the device you want to apply the parental control rule to. This is useful for restricting specific devices. |
| 6 | Target | Example: Reject | Accept: This specifies the action to take. For parental controls, you might want to use ‘Reject’ or ‘Drop’ to block traffic. |
| 7 | Weekdays | Example: Sunday | Sunday: Specify the days of the week when the rule should be active. |
| 8 | Month Days | Example: All | All: Specify the days of the month when the rule should be active. |
| 9 | Start Time (hh:mm:ss) | Example: 18:00:00 (6:00 PM) | Field must not be empty: Specify the start time when the rule should begin to apply. |
| 10 | Stop Time (hh:mm:ss) | Example: 22:00:00 (10:00 PM) | Field must not be empty: Specify the stop time when the rule should end. |
Zone Forwarding:
Zone forwarding in network configuration allows traffic to be directed from one zone to another.
To ADD new zone,
Click on “Add” in “New Zone Forward:” field.
EDIT:
Specification details are below:
| SN | Field Name | Sample Value | Description |
| 1 | Source Zone | Example options: lan, wan, etc. | --please choose--: Select the source zone from which the traffic originates. |
| 2 | Destination Zone | Example options: lan, wan, etc. | --please choose--: Select the destination zone to which the traffic is directed. |
2.6 Loopback Rule
In this page the user can configure the port where he wants to forward the traffic to. Here the user can add/edit/delete different ports as per the requirement.
The user should click on ‘add’ and then ‘edit’ to do the required changes in the port and enter the valid information in each section to configure the port for forwarding.
EDIT:
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Name | Example: loopback | Provide a descriptive name for the rule. |
| 2 | Protocol | Example: TCP+UDP | TCP+UDP: Select the protocols that the rule will apply to. |
| 3 | Source IP Address [Optional] | Example: any or a specific IP range like 192.168.1.0/24 | Optionally specify the source IP address or range. Leave empty if the rule should apply to any source IP. |
| 4 | Source Port [Optional] | Example: any | any: Specify the source port or port range from which the traffic originates. any allows traffic from all ports. |
| 5 | Loopback IP Address | Example: 127.0.0.1 | Specify the loopback IP address. Typically, this is 127.0.0.1. |
| 6 | Port | Example: any | any: Specify the destination port or port range to which the traffic is directed. any allows traffic to all ports. |
| 7 | Action | Example: DNAT | This specifies the action to take either DNAT or SNAT. |
| 8 | Internal IP Address | Example: 192.168.1.100 | Field must not be empty: Specify the internal IP address to which the traffic should be redirected. |
| 9 | Internal Port | Example: any | Redirect matched incoming traffic to the given port on the internal host. |
Once the user is done with the required configurations, should click save button and then click on the update to save the changes.
2.7 Remote Monitoring
In this page the user can select which equipment needs to be monitored remotely.
Once the user selects the type of RMS click on save.
NMS:
IN this page the user should type the server IP or domain name in the URL then click on save.
Click on upload and start (Once key is uploaded and this option is clicked, NMS automatically starts, and this router device gets registered with the NMS server provided).
TR_069:
To enable the TR_069 the user needs to click on the enable check box.
Once the user clicks on the check box of enable it will display all the required filed to configured.
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Serving Interval | 300 | A value of 300 seconds means the device will check in with the ACS (auto-configuration servers) every 5 minutes. |
| 2 | Interface | This can be something like eth0 or wan. | This specifies the network interface used for TR-069 communication. |
| 3 | Username | Example: User | The username used to authenticate with the ACS. |
| 4 | Password | •••• | The password used to authenticate with the ACS. |
| 5 | URL | http://example.com | The URL of the ACS. This is where the CPE (customer-premises equipment) will send its requests and where it will receive configurations and updates from. |
The user should fill all the required fields and click on the save button.
2.8 Tunnel
Tunnels are a method of transporting data across a network using protocols which are not supported by that network.
It is further categorised into 3 sections,
1.) General Settings
2.) GRE Tunnel
3.) IPIP Tunnel
General Settings:
In this page the user needs to select under which type of tunnel it needs to send the data.
Once the user selects the type of tunnel then click on the save button.
GRE Tunnel:
A GRE (Generic Routing Encapsulation) tunnel configuration involves setting up a virtual point-to-point connection between two endpoints over an IP network.
Here the user can add/edit/delete the details of the tunnel.
Once the required update is done then click on update to save the changes.
EDIT:
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Tunnel name | Example: GRETunnel | GRETunnel: The name of the GRE tunnel. |
| 2 | Local external IP | Example: 10.1.1.66 | The IP address of the local endpoint that will initiate the GRE tunnel. |
| 3 | Remote external IP | Example: 10.1.1.40 | The IP address of the remote endpoint that will terminate the GRE tunnel. |
| 4 | Peer tunnel IP | Example: 10.1.1.4 | The IP address of the peer's tunnel interface. |
| 5 | Local tunnel IP | Example: 10.1.1.6 | The IP address of the local tunnel interface. |
| 6 | Local tunnel net mask | Example: 255.255.255.0 | The subnet mask of the local tunnel interface. |
| 7 | Remote IP | Example: 192.168.10.0/24 | The remote network that is reachable through the GRE tunnel. |
| 8 | Enable Tunnel Link | Check to enable | Enable or disable the GRE tunnel link. |
| 9 | Interface type | Example: EWAN2 | EWAN2: The type of network interface used for the GRE tunnel. |
| 10 | MTU | Example: 1476 | 1476: Maximum Transmission Unit size for the GRE tunnel. |
| 11 | TTL | Example: 64 | 64: Time To Live value for the packets within the GRE tunnel. |
| 12 | Tunnel key | Example: 12345678 | 12345678: A unique key used to identify the GRE tunnel. |
| 13 | Enable keep alive | Check to enable | Enable or disable the keep-alive feature to monitor the tunnel's status. |
| 14 | Keep alive interval | Example: 10 | 10: Interval in seconds for the keep-alive packets. |
Once the required update is done then click on update to save the changes.
IPIP Tunnel:
An IPIP (IP-in-IP) tunnel is a simple tunnelling protocol used to encapsulate IP packets within IP packets. This is like GRE but without additional features such as keying and type fields.
Here the user can add/edit/delete the details of the tunnel.
EDIT:
Once the required update is done then click on update to save the changes.
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Tunnel name | Example: IPIPTunnel | IPIPTunnel: The name of the IPIP tunnel. |
| 2 | Local external IP | Example: 10.1.1.66 | The IP address of the local endpoint that will initiate the IPIP tunnel. |
| 3 | Remote external IP | Example: 10.1.1.40 | The IP address of the remote endpoint that will terminate the IPIP tunnel. |
| 4 | Peer tunnel IP | Example: 10.1.1.4 | The IP address of the peer's tunnel interface. |
| 5 | Local tunnel IP | Example: 10.1.1.6 | The IP address of the local tunnel interface. |
| 6 | Local tunnel net mask | Example: 255.255.255.0 | The subnet mask of the local tunnel interface. |
| 7 | Remote IP | Example: 192.168.10.0/24 | The remote network that is reachable through the IPIP tunnel. |
| 8 | Enable Tunnel Link | Check to enable | Enable or disable the IPIP tunnel link. |
| 9 | Interface type | Example: EWAN2 | EWAN2: The type of network interface used for the IPIP tunnel. |
| 10 | MTU | Example: 1476 | 1476: Maximum Transmission Unit size for the IPIP tunnel. |
| 11 | TTL | Example: 64 | 64: Time To Live value for the packets within the IPIP tunnel. |
| 12 | Tunnel key | Example: 12345678 | Although typically not used in IPIP, this field might be included for compatibility with certain configurations. |
| 13 | Enable keep alive | Check to enable | Enable or disable the keep-alive feature to monitor the tunnel's status. |
| 14 | Keep alive interval | Example: 10 | 10: Interval in seconds for the keep-alive packets. |
3.Maintenance
In this module the user can configure/upgrade/modify the settings related to system, password,
firmware and monitoring.
It includes 6 submodules.
- General
- Password
- Reboot
- Import and Export config
- Firmware upgrade
- Monitor Application
3.1 General
Here you can configure the basic aspects of router like its hostname or the timezone.
It is further sub-divided into,
1.) General Settings
2.) Logging
3.) Language and Style
General Settings:
EDIT:
| SN | Field Name | Sample Value | Description |
| 1 | Local Time | 2024/07/30 13:25:47 | The current local date and time set on the device. |
| 2 | Hostname | 22B25240007 | The hostname of the device, which is used to identify it on the network. |
| 3 | Timezone | Asia/Kolkata | The timezone setting of the device, which determines the local time. |
Once the user configures the required details then click on the save button to save all the details.
Logging:
Here the user can configure the basic aspects of your device related to system.
The system log configuration provided specifies how the device handles and stores log information, including buffer size, external log server details, and log verbosity levels.
EDIT:
| SN | Field Name | Sample Value | Description |
| 1 | System log buffer size | Example: 32 kiB | The size of the memory buffer allocated (0-32) for storing system logs before they are either written to a file or sent to an external server. |
| 2 | External system log server | Example: 0.0.0.0 | The IP address of an external server where logs can be sent. |
| 3 | External system log server port | Example: 514 | The port used to send logs to the external log server. Port 514 is the default port for syslog. |
| 4 | Log output level | Example: Debug | Sets the detail level of the system logs. |
| 5 | Cron Log level | Example: Debug | The detail level of the logs for cron jobs. |
Once the user configures the required details then click on the save button to save all the details.
Language and Style:
Here the user can configure the basic aspects of your device related to language.
Once the user configures the required details then click on the save button to save all the details.
3.2 Password
In this module the user can set the password for the admin credentials.
Specifies the password for the guest account. If the user enters a plaintext password here, it will get replaced with a crypted password on save. The new password will be effective once the user logs out and log in again.
3.3 Reboot
In this module the user can reboot the device remotely.
First option is to directly reboot the device without enabling the maintenance reboot tab.
Click on “Reboot Now” at the bottom of the screen to start the reboot process.
To start maintenance reboot process first the user needs to fill all the required fields.
Need to select the type of reboot for the device whether it needs to be Hardware or Software reboot.
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Enable Maintenance Reboot | Enable/Disable | Indicates whether the maintenance reboot feature is enabled or not. |
| 2 | Type | Maintenance Reboot | Specifies the type of reboot being scheduled. |
| 3 | Reboot Type | Software/Hardware | Hardware: A hardware reboot involves restarting the entire device as if it were powered off and on again.
Software: A software reboot involves restarting the operating system without powering off the hardware. |
| 4 | Minutes | Example: 59 | The minute at which the reboot should occur (0-59). |
| 5 | Hours | Example: 22 (10 PM) | The hour at which the reboot should occur (0-23, in 24-hour format). |
| 6 | Day Of Month | Example: All | Specifies which days of the month the reboot should occur (1-31). "All" means it will occur every day. |
| 7 | Month | Example: All | Specifies which months the reboot should occur (1-12). "All" means it will occur every month. |
| 8 | Day Of Week | Example: All | Specifies which days of the week the reboot should occur (0-6, where 0 is Sunday). "All" means it will occur every day of the week. |
Once the user fills all the required given parameters click on the save.
3.4 Import and Export
In this section, User can Import & Export Configuration files of the Device.
Click “Export Config” to export device configuration & settings to a text file,
Click “Import Config” to import device configuration & settings from a previously exported text file.
The user needs to select on the “choose file”, upload the required file and click on apply.
3.5 Firmware Upgrade
The user can upgrade with the latest software for the existing firmware.
Click on the flash image and chose the path where the sys-upgrade file is kept and then click on flash image, it will upgrade to the latest software once the reboot is done.
This option will completely reset the device to default settings.
Click on the Retain Config and flash and chose the path where the sys-upgrade file is kept and then click on Retain Config and flash, it will upgrade to the latest software once the reboot is done.
This refers to updating the firmware (flashing) of a device while preserving the current configuration settings.
Click on the Factory Reset for the complete retest of the device.
3.6 Monitor Application
In this section, the monitor application is divided into major 2 configurations which is further sub-divided into 4 editable options,
1.) Modem Monitor Application Configuration:
2.) Router Monitor Application Configuration:
Modem Monitor Application Configuration:
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Enable Ping Check Application | Enable/Disable | Turns on the functionality to perform ping checks on specified IP addresses. |
| 2 | Time Interval for Check (In minutes) | Example: 10 minutes | Frequency at which the ping checks are performed. |
| 3 | Select No of IP addresses to ping | Example: 1 | Number of IP addresses that will be pinged. |
| 4 | IP Address 1 | Example: 8.8.8.8 | The IP address to ping. |
| 5 | No. of Retries | Example: 5 | Number of times to retry pinging an IP address if the initial ping fails. |
| 6 | Failure Criteria in (%) | Example: 80% (If 4 out of 5 pings fail, it’s considered a failure) | Percentage of failed pings required to consider the ping check a failure. |
| 7 | Action On Failure | Example: Restart Modem | Action to be taken if the ping check fails according to the criteria. |
| 8 | Enable Second Level Action | Enable/Disable | Option to enable a secondary action if the primary action fails multiple times. |
| 9 | Second Level Action Threshold | Example: 2 | Number of failures required to trigger the secondary action. |
| 10 | Second Level Action | Example: Restart Board (Reboots the entire hardware board) | The action to be taken if the second level action threshold is met. |
Save the details once made necessary changes.
Router Monitor Application Configuration:
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Enable Ping Check Application | Enable/Disable | Activates the ping check functionality to monitor router performance. |
| 2 | Time Interval for Check (In minutes) | Example: 10 minutes | How frequently the ping checks are performed. |
| 3 | Select No of IP Addresses to Ping | Example: 1 (Please select the appropriate number based on your requirements) | Choose the number of IP addresses to ping. This typically involves selecting from a list or entering multiple addresses. |
| 4 | No. of Retries | Example: 3 | Number of retries if a ping fails. |
| 5 | Failure Criteria in (%) | Example: 80% (If 80% of the pings fail, it’s deemed a failure) | Percentage of failed pings required to consider the ping check as failed. |
| 6 | Action On Failure | Example: Restart IPsec | The action taken if the ping check fails according to the criteria. |
| 7 | Enable Second Level Action | Enable/Disable | Option to enable an additional action if the primary action fails. |
| 8 | Second Level Action Threshold | Example: Specify the number of failures, such as 2 | Number of times the primary action must fail before the secondary action is triggered. |
| 9 | Second Level Action | Example: Restart Board | The action to be taken if the second level action threshold is met. |
Save the details once made necessary changes.
4.Status
In this module the user can view the status of the router device with respect to the network, Wan, modem etc.
It has 4 submodules.
- Interfaces
- Internet
- Modem
- Routes
4.1 Interfaces
Each network device (interface) is associated with specific traffic statistics, uptime, and status. Active interfaces are operational, while inactive interfaces are not currently transmitting data.
Looking on the network status the user can check if the cellular, wifi, ewan, vpn etc is up.
4.2 Internet
In this submodule the user can view the status of the internet connections.
To see the latest status of the internet connection the user needs to click on the refresh button.
4.3 Modem
This modem status page provides comprehensive information about the cellular connection's network operator, technology, mode, and various signal quality metrics.
4.4 Routes
This configuration shows how the router directs traffic between different networks and interfaces, ensuring proper communication within the local network and to external networks via the default gateway.
ARP Table: Maps IP addresses to MAC addresses for devices on the network, helping in identifying which device is on which interface.
IPv4 Routes: This shows which network is directly connected on which interface.
Example: Network 192.168.10.0/24 is directly connected on interface eth0.1.
IPv6 Routes: Similar routes as IPv4, but this time listed under IPv6 routing rules.
Example: Local networks 192.168.10.0/24 and 192.168.100.0/24 are managed through eth0.1 and ra0, respectively.
5. Features
In this module the user can see all the features that the router device has.
This module includes 7 features.
- Mac Address Binding
- URL Filtering
- Web Server
- Wi-Fi MacID Filtering
- Routing
- Others
5.1 Mac Address Binding
MAC address binding is a configuration that binds a specific MAC address to a specific IP address. This ensures that a particular device on the network always receives the same IP address from the DHCP server, which can be useful for network management, security, and ensuring consistent network behaviour.
Under this submodule the user can configure/update/edit the IP Address for MAC.
You can edit the pre-existing configuration, or you can ‘Add’ in the ‘New MAC ADDRESS’ field.
EDIT:
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Device Name | Macbinding1 | A user-defined name for the binding configuration. |
| 2 | MAC Address | 48:9e:bd:da:45:91 | The unique identifier for the network interface of the device to which the IP address will be bound. |
| 3 | IP Address | 192.168.10.55 | The IP address that will be consistently assigned to the device with the specified MAC address. |
By applying this configuration, the DHCP server will always assign the IP address 192.168.10.55 to the device with the MAC address 48:9e:bd:da:45:91, ensuring consistency and stability in network addressing for that device.
- Once the user modifies the MAC address /IP Address then click on the save button to save the changes done.
- The user can click on the deleted button to delete an existing configured device.
Post all the changes the user needs to click on the update to reflect all the changes in the application.
5.2 URL Filtering
In this submodule the user should provide the URL which needs to be blocked for the device. By implementing URL filtering with the specified URL, you can control and restrict access to certain websites, thereby improving network security and managing user access.
To add the new URL for blocking, click on the Add New button.
Once the user clicks on the Add New button a new pop will appear in that page write the URL and click on the save.
The user can select the status of that URL while defining the URL.
To edit / delete the existing URL the user needs to click on the edit /deleted button respectively.
Click on “save” after the changes are done as per the need.
5.3 Web Server
This configuration will allow your device to serve web traffic securely over HTTPS, keep its system time synchronized, and ensure that all HTTP traffic is redirected to HTTPS for better security.
EDIT:
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Enable HTTP | HTTP Port: 80
Enable or disable the HTTP server. |
Port 80 is the default port for HTTP traffic. It is used to serve web pages over an unencrypted connection. |
| 2 | Enable HTTPS | HTTPS Port: 443
Enable or disable the HTTPS server. |
Port 443 is the default port for HTTPS traffic. It is used to serve web pages over an encrypted connection. |
| 3 | Redirect HTTPS | Option to redirect HTTP traffic to HTTPS. | When enabled, all HTTP requests will be automatically redirected to the HTTPS port to ensure secure communication. |
| 4 | Enable NTP Sync | Enable or disable NTP synchronization. | Synchronizes the device’s system clock with an external NTP server to maintain accurate time. |
| 5 | NTP Server | 0.openwrt.pool.ntp.org | The address of the NTP server used for time synchronization. The openwrt.pool.ntp.org server is a public NTP server pool. |
| 6 | NTP Sync Interval (In Minutes) | 15 | The interval at which the device will sync its clock with the NTP server, set to every 15 minutes in this case. |
Click on save once changes are made.
5.4 Wi-Fi MacID Filtering
Wireless MAC ID Filtering allows you to control which devices can connect to your wireless network based on their MAC (Media Access Control) addresses. This can help enhance security by allowing only specified devices to access the network.
It is further divided into 2 categories,
WIFI 2.4G AP
WIFI 2.4G AP Guest
Before adding the MacIDs the user needs to select the mode from the dropdown menu.
In ‘Change Mode’ select one option,
Blacklist
In blacklist mode, you specify which MAC addresses are not allowed to connect to the wireless network. Devices not on the blacklist will be able to connect.
Whitelist
In whitelist mode, you specify which MAC addresses are allowed to connect to the wireless network. Devices not on the whitelist will be blocked.
To Add the MacID the user needs to click on Add New option.
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Status | Enable/Disable | Enable or disable the MAC ID filtering. |
| 2 | MAC ID | Example: e8:6f:38:1a:f2:61 | The MAC address of the device to be whitelisted or blocklisted. |
| 3 | Network Name | Example: WIFI 2.4G AP or Wi-Fi 2.4G AP Guest. | The network to apply the MAC ID filtering. |
Once the required MAC ID and Network Name is configured the user needs to click on the save button to add the details.
The user needs to click on the edit button to do modifications on the pre-existing configuration.
Once the required MACID / Network Name is modified the user needs to click on the save button to reflect the changed value in the application.
5.5 Routing
In this submodule the user can configure the parameters related to routing of the device like Target address, Networks address etc. Routing configurations allow network packets to be directed between different subnets and networks.
It is further divided into 2 sections,
Static IPV4 Routes
Advanced Static IPV4 Routes
Static IPV4 Routes:
Click on ‘Add’ to add a new interface.
EDIT:
To edit the existing device the user needs to click on the edit option.
Once the changes are done click on the save button to save all the changes.
Click on the deleted button to delete the existing device detail.
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Interface | Ex: eth0.1 | The network interface to be used for this route. Select the one to use from dropdown. |
| 2 | Target | Ex: 192.168.20.0 | The destination subnet to which traffic should be routed. |
| 3 | IPv4 Netmask | 255.255.255.0 | The subnet mask for the target network. |
| 4 | Metric | 0 | The priority of the route.
Lower values indicate higher priority. |
| 5 | IPv4 Gateway | Ex: 192.168.10.1 | The gateway IP address to be used for routing traffic to the target subnet. |
| 6 | Route Type | Unicast | Standard route for individual destination IP addresses.
Custom changes can be made. |
Click on save once configuration changes have been made.
Advanced Static IPV4 Routes:
Click on ‘Add’ to add a new interface.
EDIT:
To edit the existing device the user needs to click on the edit option.
Once the changes are done click on the save button to save all the changes.
Click on the deleted button to delete the existing device detail.
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Interface | Ex: ra0 | The network interface through which the traffic will be routed. Select as per requirement. |
| 2 | To | Ex: 192.168.10.1 | This is the target address to which the traffic is being directed. In this case, all traffic destined for 192.168.10.1 will follow this route. |
| 3 | IPv4 Netmask | 255.255.255.192 | This defines the subnet of the destination address. |
| 4 | Table | 1.) Local
2.) Main 3.) Default 4.) 220 5.) custom |
1.) This table contains local routes for the addresses assigned to the local interfaces. It's typically used for host and broadcast addresses.
2.) The primary routing table used by the system. 3.) A fallback table used when no other table is specified. 4.) Often used for policy-based routing. 5.) A user-defined routing table. |
| 5 | From | Ex: 192.168.100.1 | This source address restricts the route to traffic originating from 192.168.100.1. Traffic from other sources won't use this route. |
| 6 | Priority | 20 | The priority value determines the preference of this route. A lower number means higher priority; 20 is relatively high, so this route will be preferred over routes with higher priority values. |
Once all the configurations are done click on the update button to reflect the changes made.
5.6 Others
In this page the user will get to do all the other miscellaneous configuration with respect to the device based on the required parameters. Each utility serves a specific purpose, providing various functionalities for managing and troubleshooting network configurations and statuses.
Specification details are given below:
| SN | Field Name | Sample Value | Description |
| 1 | Set Date | Date and time fields (day, month, year, hour, minute, second) | Sets the system date and time to the specified values. |
| 2 | Get Date | System | Retrieves and displays the current system date and time. |
| 3 | ipsec status all | Command ‘Get’ | Displays the status of all IPsec connections. |
| 4 | Wi-Fi Scan | Command ‘Get’ | Initiates a scan for available Wi-Fi networks. |
| 5 | iPerf3 Client | IP address (e.g., 192.168.10.100) | Runs an iPerf3 client to measure network performance. |
| 6 | iPerf3 Server | Command ‘Run’ | Runs an iPerf3 server to measure network performance. |
| 7 | Ping | IP address or domain (e.g., 8.8.8.8) | Sends ICMP echo requests to the specified address to check connectivity. |
| 8 | traceroute | IP address or domain (e.g., 8.8.8.8) | Traces the route packets take to reach the specified address. |
| 9 | NTP Sync | Command ‘Sync’ | Synchronizes the system time with the configured NTP server. |
| 10 | Download Files | File or database identifier | Initiates a download of the specified file or database. |
| 11 | Restart Power | Command ‘Restart’ | Restarts the power of the device. |
| 12 | Restart Modem | Command ‘Restart’ | Restarts the modem. |
| 13 | Run AT Command | Enter AT command | Executes the specified AT command on the modem. |
| 14 | Show Board Configuration | Command ‘Show’ | Displays the current board configuration. |
| 15 | Show VPN Certificate Name | Command ‘Show’ | Displays the name of the VPN certificate in use. |
| 16 | Switch SIM to Secondary (Takes >2 mins) | Command ‘Run’ | Switches the active SIM to the secondary SIM card. |
| 17 | Send test SMS | Phone number (e.g., +911234567890) message text (e.g., "Hello how are you?") | Sends a test SMS to the specified phone number. |
| 18 | ReadlatestSMS | Command ‘Read’ | Reads the most recent SMS received by the device. |
| 19 | Data Usage | From: Start date (YYYY-MM-DD)
To: End date (YYYY-MM-DD) |
Displays data usage statistics for the specified date range. |
| 20 | Monthly Data Usage | Month: Month (e.g., 07)
Year: Year (e.g., 2024) |
Displays data usage statistics for the specified month and year. |
| 21 | Modem Debug Info | Command ‘Read’ | Displays debug information for the modem. |
| 22 | Scan Network operators (Takes >3 mins) | Command ‘Scan’ | Initiates a scan for available network operators. |
| 23 | Network operator list (First Perform Scan Network Operators) | Command ‘Show’ | Displays the list of network operators detected in the previous scan. |
| 24 | ReadLogFiles | Log file identifier | Reads and displays the specified log file |
| 25 | Enable ssh (Admin) | Command ‘Run’ | Enables SSH access for the admin user. |
| 26 | Disable ssh (Admin) | Command ‘Run’ | Disables SSH access for the admin user. |
| 27 | ClearSIM1Data | Command ‘Clear’ | Clears data usage statistics for SIM1. |
| 28 | ClearSIM2Data | Command ‘Clear’ | Clears data usage statistics for SIM2. |
| 29 | Create Bridge with SW_LAN | Network interface identifier | Creates a network bridge with the specified interface and SW_LAN. |
| 30 | Show Bridge | Command ‘Show’ | Displays information about the current network bridges. |
| 31 | Delete Bridge | Command ‘Delete’ | Deletes the specified network bridge. |
| 32 | Output | Any value | Displays output for all the above actions. |
6.Logout
The user should click on log out option to logged out from the router application.